Governments across major economies are now setting structured rules for digital asset custody and reporting. Any serious entrant must design compliance into the core architecture rather than add it later. That shift is steadily increasing demand for crypto custody platforms across banks and fintech institutions.
These institutions require regulated storage providers with segregated accounts and transparent audit trails. They may also expect insured asset protection and verifiable reserve controls before allocating capital. A properly engineered custody system must integrate cold storage governance and encrypted key management. It should also enforce policy-based transaction approvals, with real-time monitoring and AML screening, to meet regulatory requirements.
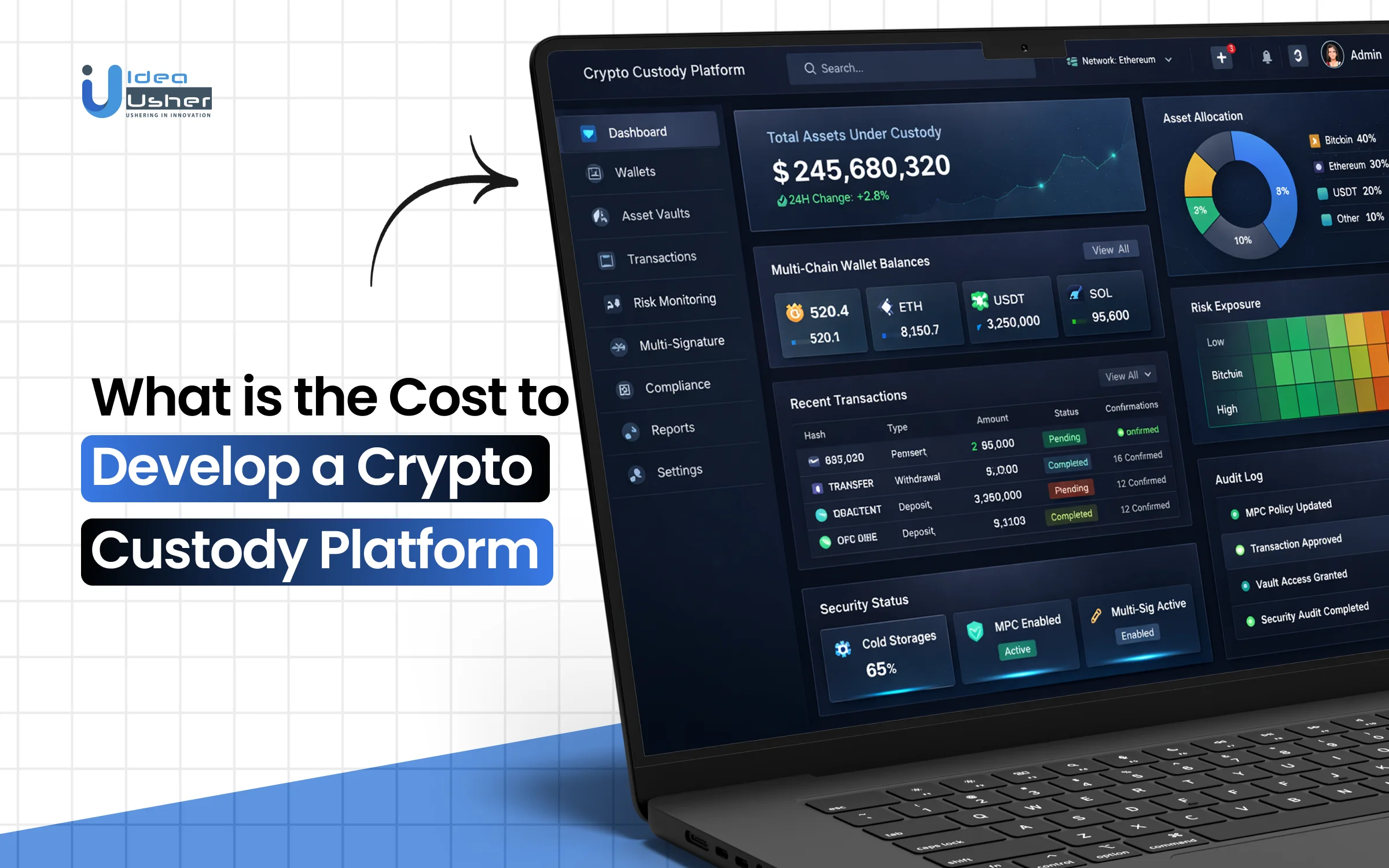
Over the years, we’ve developed numerous crypto custody solutions that leverage technologies such as multi-party computation-based key management and HSM-based cryptographic infrastructure. As we have this expertise, we’re sharing this blog to discuss the cost to develop a crypto custody platform.
Key Market Takeaways for Crypto Custody Platforms
According to Research and Markets, the crypto custody market is expanding steadily as institutions move from experimentation to structured allocation. Growth from 3.28 billion dollars in 2025 to a projected 7.74 billion dollars by 2032 signals that secure storage is no longer optional infrastructure. As regulatory clarity improves and risk frameworks mature, institutions are allocating capital to digital assets with greater confidence.
Source: Research and Markets
After major exchange failures, institutions are no longer comfortable leaving large balances on trading platforms. They are demanding segregated cold storage, multi-signature governance, geographic key distribution, and insured coverage structures. Modern custody platforms also support staking and governance participation, allowing institutions to generate yield while maintaining compliance and security oversight.
Established players are strengthening trust through regulation and insurance-backed models. Coinbase Custody operates under NYDFS oversight with insured cold storage and institutional staking services.
BitGo continues to lead in multi-signature architecture and insured custody programs, and partnerships such as Deutsche Bank working with Bitpanda and Taurus show how traditional banks are formally integrating institutional-grade crypto custody into their future infrastructure plans.
What Is a Crypto Custody Platform?
A crypto custody platform securely stores and manages digital assets for users or institutions. It protects private keys using technologies such as multi-signature wallets and MPC to reduce the risk of theft. These platforms are commonly used by exchanges, funds, and fintech apps to ensure secure and compliant asset management.
Standout Features of a Crypto Custody Platform
What truly differentiates an institutional-grade custody platform is its pairing of hardened asset protection with programmable control frameworks that institutions can confidently manage. Users should be able to stake assets directly from custody, simulate governance policies before activation, and instantly assess counterparty risk during withdrawals.
1. One Click Staking
Users do not want to shift assets across platforms just to earn yield; they expect rewards to be generated directly inside custody. A simple activate-staking toggle next to ETH, SOL, or DOT balances enables auto-accrual without requiring validator research or external dashboards.
Why Users Love It: It generates passive rewards without adding operational steps.
Example Platform: Coinbase Custody integrates native staking directly within its custody interface for supported assets.
2. Policy Simulation Mode
Treasury teams need to understand consequences before enforcing governance changes. A simulation layer allows testing of a 4-of-7 multisig with a 24-hour time lock against a live-sized transaction before committing the rule on-chain.
Why Users Love It: It prevents costly mistakes before funds ever move.
Example Platform: Fireblocks provides policy engines and workflow simulations for institutional treasury controls.
3. Counterparty Risk Scoring
Address-level intelligence should surface risk instantly at the point of withdrawal. When a destination wallet is pasted, the interface dynamically classifies it as low-, medium-, or high-risk based on regulatory flags and exploit databases.
Why Users Love It: It adds a real-time safety check without slowing transactions.
Example Platform: BitGo integrates risk monitoring and wallet screening into its custody workflows.
4. Transaction Timeline View
Institutions require contextual clarity rather than simple status labels. A visual timeline displays the proposal origin, required approvals, time-lock countdown, and execution stage in a structured sequence.
Why Users Love It: It replaces uncertainty with complete visibility.
Example Platform: Anchorage Digital provides detailed approval tracking and transaction-governance visibility.
5. Reusable Allowlists
Operational efficiency improves when frequent counterparties are predefined and policy-bound. Saved allowlists can auto-populate destination details and enforce preset approval thresholds for vendors, exchanges, or payroll wallets.
Why Users Love It: It reduces manual errors and saves time on repetitive transfers.
Example Platform: Copper supports whitelisted withdrawal addresses and policy-bound transfer controls.
6. Audit Mode
Regulators and compliance officers require visibility without transactional authority. A segregated read-only environment enables access to balances, transaction logs, and policy history without initiation privileges.
Why Users Love It: It simplifies compliance reviews without compromising security.
Example Platform: Gemini Trust Company offers segregated reporting and audit access for institutional clients.
7. Emergency Pause Button
Incident response must be immediate and decisive during compromise events. A centrally governed halt control can suspend all outgoing transactions across approval queues and batches in real time.
Why Users Love It: It provides instant control during critical situations.
Example Platform: Ledger Enterprise enables governance-level transaction freezes and emergency controls for enterprise clients.
How Does the Crypto Custody Platform Work?
A crypto custody platform securely generates and stores private keys within hardened infrastructure that can resist breaches. It will enforce policy-based approvals with hardware-backed signing, ensuring transactions execute only after verified intent. The system also monitors activity in real time, enabling institutions to confidently manage digital assets under strict governance.
1. Key Generation: The Birth of Ownership
Before any asset can be custodied, the platform must create the mathematical proof of ownership, the private key.
How it actually works:
In a consumer wallet, a single private key is generated on a device. In institutional custody, the key should never exist as a complete whole.
The Process:
- Multiple independent servers generate random entropy simultaneously
- Using Multi-Party Computation (MPC), these entropy sources collaborate to produce key shards
- Each shard lives on a separate, geographically distributed machine
- No single machine ever possesses the full private key
- The full key is never assembled in memory, even for a microsecond
The client sees a wallet address on the blockchain that represents ownership. The platform holds cryptographic key fragments that must securely collaborate to produce a valid signature. Only after policy checks are satisfied can the transaction be signed and executed.
2. Deposit: Watching the Chain
When a client receives assets, the custody platform doesn’t “accept” a transfer—it detects one.
The Infrastructure:
- Blockchain nodes (Bitcoin Core, Geth, Solana RPCs) run continuously
- Node clusters monitor the mempool and new blocks
- When a transaction arrives at the client’s published address, the node detects it
- The platform waits for block confirmations (6 for BTC, 15-20 for ETH, etc.)
- Only after finality depth is reached is the deposit credited to the client’s internal ledger
The Hidden Complexity:
If a block is reorganized, the system must quickly detect it because a deposit can disappear. It must also correctly handle UTXO logic and account-based balance models. At scale, the platform should accurately index transactions so each event maps to the right client account.
3. Asset Protection: The Custody Layer
This is where institutional custody separates from self-custody.
The Three States of Assets:
| State | Definition | Security Level | Use Case |
| Cold Storage | Keys are completely offline. Air-gapped. | Maximum | Long-term reserves, 90%+ of assets |
| Warm Storage | Keys online but require multiple approvals, time-locks, and policy checks | Medium-High | Daily treasury operations, staking |
| Hot Storage | Keys online, automated signing | Lower | Withdrawal processing, exchange integrations |
The Orchestration:
- Assets move between states based on programmable business logic
- A withdrawal request triggers a policy engine evaluation
- Policy checks: Is this address whitelisted? Is the amount within daily limits? Is the requester authorized?
- Only after policy approval do the key shards begin the signing process
4. Signing: The Cryptographic Ceremony
When a transaction is approved, the platform must prove ownership on the blockchain without ever exposing the private key.
The MPC Signing Process:
- Transaction construction – The platform builds the raw transaction (recipient, amount, fee, nonce)
- Message hash – The transaction is hashed into a fixed-length digest
- Shard collaboration – Each key shard independently computes a partial signature
- Signature aggregation – The partial signatures combine to form a complete, valid ECDSA or Ed25519 signature
- Broadcast – The signed transaction is pushed to the blockchain network
Critical Detail: The shards communicate during signing, but never reveal their individual secrets to each other. The math ensures that the full signature is valid without the full key ever existing.
5. Policy Enforcement
A signature alone is not sufficient for institutional security. The system must embed enforceable rules directly into the cryptographic signing flow so approvals are validated before execution. This approach ensures that transactions can proceed only when predefined governance and policy controls are satisfied.
How this is enforced:
- The policy engine is integrated into the signing protocol
- Key shards refuse to participate in signing unless policy conditions are met
- No database bypass is possible; the cryptography itself enforces governance
6. Withdrawal: Settlement Finality
Once a transaction is signed and broadcast, the custody platform must continue to monitor its lifecycle. It should track confirmations and detect reorg risks to enable settlement to be finalized with confidence. The system may also reconcile balances and update internal ledgers to ensure accounting integrity.
The Withdrawal Lifecycle:
- Transaction broadcast to the blockchain mempool
- Platform monitors for inclusion in a block
- The platform waits for the confirmation threshold
- Internal ledger updates: client balance decreased
- Transaction hash recorded for audit trail
- Client notified of completion
The Anxiety Point: Between broadcast and confirmation, the transaction is pending but not final. If the network is congested, fees are set too low, or a chain reorg occurs, the transaction may fail, and assets must be made available again.
Cost Required to Develop a Crypto Custody Platform
Building an institutional crypto custody platform demands careful engineering across security and compliance layers. We develop these systems using a cost-effective, phased approach that keeps infrastructure lean while meeting enterprise-grade standards.
Cost Summary by Project Tier
| Tier | Estimated Total Cost | Timeline | Best For |
| MVP (Beta) | $100k – $200k | 4–6 Months | Seed stage, internal testing. |
| Standard Enterprise | $250k – $550k | 8–12 Months | Regional firms, fund managers. |
| Global Institutional | $700k – $1.5M+ | 14+ Months | Banks, prime brokers, global exchanges. |
This step-by-step cost breakdown shows where the budget is actually spent when building an institutional crypto custody platform. It breaks the build into core phases so users can plan scope, security, and timelines with clear expectations.
1. DKG & MPC Layer
| Component | Estimated Cost | Notes |
| Design & Research | $15k – $30k | Architecture blueprints, DKG protocol selection |
| Protocol Development | $40k – $80k | Implementing GG20 / CMP MPC protocols |
| Security Hardening | $20k – $40k | Key refresh logic, quorum configurations |
| External Crypto Audit | $30k – $60k | Mandatory for institutional credibility |
| Estimated Phase Total | $105k – $210k | Core cryptographic foundation |
2. Policy Engine
| Component | Estimated Cost | Notes |
| Rule Engine Logic | $20k – $35k | Time-locks, velocity controls, transaction limits |
| Role-Based Access Control (RBAC) | $15k – $25k | Multi-approval workflows |
| MPC Integration | $25k – $40k | Pre-signature policy enforcement |
| Estimated Phase Total | $60k – $100k | Governance and transaction authorization layer |
3. Chain Monitoring
| Component | Estimated Cost | Notes |
| Node Setup (3+ Chains) | $10k – $25k | BTC, ETH, SOL full nodes |
| Reorg & Finality Logic | $15k – $30k | Fork detection, confirmation depth logic |
| Monthly Hosting | $1,500 – $5,000/mo | Cloud infrastructure for high-performance nodes |
| Estimated Phase Total (Initial Build) | $25k – $55k | Excluding recurring hosting |
4. Secure Infrastructure
| Component | Estimated Cost | Notes |
| HSM Procurement / Cloud Leasing | $10k – $50k | AWS CloudHSM or physical devices |
| Environment Isolation (TEE / SGX) | $20k – $45k | Secure enclave development |
| Geographic Redundancy | $15k – $30k | Multi-region failover shards |
| Estimated Phase Total | $45k – $125k | Physical and hardware security layer |
5. Compliance & AML
| Component | Estimated Cost | Notes |
| Integration Development | $10k – $20k | API integration for Chainalysis / Sumsub |
| Real-Time Risk Scoring | $15k – $30k | Automated freeze and flag logic |
| Licensing Fees (Legal) | $50k – $150k+ | MiCA, MTL, VARA, jurisdiction dependent |
| Estimated Phase Total | $75k – $200k+ | Regulatory and compliance infrastructure |
6. Settlement & Liquidity
| Component | Estimated Cost | Notes |
| Exchange API Integration | $20k – $50k | Binance, Coinbase, institutional venues |
| Proof of Reserve Modules | $15k – $35k | Merkle tree or zk-based attestations |
| Collateral Locking Logic | $20k – $40k | Smart contract or ledger-based escrow |
| Estimated Phase Total | $55k – $125k | Market connectivity layer |
This estimate reflects a typical institutional build and may vary based on jurisdiction, feature depth, and security requirements. The total estimated cost generally ranges between $250,000 to $800,000 USD, depending on scope and compliance complexity.
For a more precise quote aligned to your custody model and regulatory strategy, feel free to connect with us for a free consultation.
Factors Affecting the Cost of a Crypto Custody Platform
The cost of a crypto custody platform primarily depends on your cryptographic architecture, multi-chain support, and the complexity of your policy engine. If you implement advanced threshold signing and programmable compliance, development and audits will likely increase significantly.
1. Cryptographic Architecture Choice
MPC vs. HSM vs. Hybrid Threshold Signatures
This is the single most consequential decision in your entire build. It determines not just security but governance flexibility, recovery workflows, and future upgradeability.
What most people miss: Implementing MPC from scratch is not just expensive, it is risky. One misstep in the Distributed Key Generation DKG protocol and your secure sharding scheme leaks entropy.
Your options:
- Full in-house MPC protocol implementation: Requires cryptography PhDs or engineers who have broken things before fixing them. Extensive audits are mandatory.
- Licensed MPC frameworks: Faster time to market, but vendor lock-in and opaque black boxes.
- HSM-backed custody: FIPS 140-2 certified but rigid. Great for Bitcoin. Painful for Cosmos staking.
Cost Impact: +$80k to $200k
Depending on the audit depth and whether you build or license.
2. Number of Supported Blockchains
BTC and ETH are table stakes. Everything else is complexity.
Supporting Bitcoin and Ethereum is a solved problem. But in 2026 institutions expect multi-chain support and each chain is a unique snowflake of suffering.
The hidden costs no one tells you about:
| Chain | Signature Scheme | Node Infrastructure | Special Hell |
| Bitcoin | ECDSA | Full node | UTXO accounting |
| Ethereum | ECDSA | Execution and Consensus clients | Reorg handling |
| Solana | Ed25519 | RPC nodes | Transaction state expiry |
| Cosmos | Ed25519 | Tendermint RPC | IBC transfers |
| Starknet | STARK | Sequencer dependent | L1 to L2 messaging |
What actually happens: Each chain requires its own transaction construction logic, fee estimation engine, monitoring dashboards, and wallet derivation path standards. Then you test. Then you audit. Then you support it at 3 AM.
Cost Impact: +$15k to $40k per additional chain.
Solana and Cosmos sit at the high end. EVM L2s are cheaper but not free.
3. Institutional Policy Engine Complexity
The depth of your policy engine defines how precisely transaction rules can be configured across different users, entities, and asset classes, shaping both governance flexibility and control enforcement.
As approval rules, time locks, velocity limits, and compliance logic become more advanced, engineering effort and audit depth increase accordingly.
Where complexity compounds:
- Time-locked withdrawals: Not just a delay. The transaction must be constructible, cancellable, and auditable during the pending window.
- Velocity controls: Daily volume limits. Per asset limits. Per user limits. Per destination limits.
- Programmable compliance: Automatically block addresses flagged by OFAC or internal risk models.
- Multi-entity workflows: Subsidiaries with separate treasuries reporting to a parent with consolidated oversight.
Cost Impact: +$40k to $120k.
Heavy customization and audit logic drive the high end.
4. Proof of Reserves and Audit Transparency
Custody platforms must enable cryptographic verification that the total assets held accurately match recorded user liabilities in real time, providing mathematically provable solvency rather than relying on trust or periodic reports.
As platforms move toward automated attestations and zero-knowledge solvency proofs, infrastructure complexity and continuous computation requirements increase significantly.
The engineering lift:
- Merkle attestations: Generating a verifiable inclusion proof for thousands of user balances without exposing individual positions.
- zk Solvency proofs: Zero-knowledge proofs that total liabilities are less than or equal to total assets without revealing any balances.
- Automated reporting dashboards: Real-time solvency visualizations for institutional clients and regulators.
The hard part: This is not a one-time script. It is a continuous automated pipeline that must remain performant as user counts grow. Every withdrawal triggers a new Merkle root. Each audit cycle requires fresh proof.
Cost Impact: +$25k to $75k.
zk proofs sit at the premium end. Merkle trees are cheaper but require careful index engineering.
5. Off-Exchange Settlement and Liquidity Integration
This capability allows institutions to trade across external venues while retaining asset control within their custody environment, reducing counterparty exposure without sacrificing market access.
Implementing collateral locking, reconciliation engines, and exchange-level API integrations can significantly increase backend complexity and operational risk management requirements.
What this actually requires:
- Exchange API deep dives: Each exchange uses a different collateral-verification mechanism. Some require on-chain proofs. Some accept signed API assertions. Some have no programmatic off-exchange settlement.
- Collateral locking logic: When a client initiates a trade, their assets are marked as encumbered in your internal ledger. No double spending. No over-committing.
- Reconciliation engines: Your ledger and the exchange ledger must remain in sync. Trades settle. Collateral unlocks. Sometimes exchanges get the math wrong.
Cost Impact: +$50k to $150k.
Depends entirely on the number of exchanges and the level of automation involved.
Can a Custody Platform Refresh or Rotate Keys Without Moving Assets?
Yes, a crypto custody platform can refresh or rotate keys without moving assets if it uses advanced cryptographic architecture. With MPC resharing or HSM key wrapping, the underlying private key remains logically consistent, while the old key material becomes unusable. The blockchain address remains unchanged, and assets remain untouched while security is proactively strengthened.
The Core Problem: Keys Do Not Expire
Unlike a credit card number, which you can cancel and reissue, a blockchain private key is permanent. If the key exists today, it exists forever. If a shard, a backup, or a memory fragment is stolen today but not used until 2027, the theft is still viable.
The industry’s dirty secret is this. Most custody platforms in 2024 generated keys once and assumed they would never leak.
But 2026 is the year of Proactive Secret Sharing.
How Key Refresh Works Without Moving Assets
This is where the magic happens and where most vendors fail to explain it clearly.
The Analogy: The Broken Padlock
Imagine a padlock securing a warehouse. The key is held by three trustees. If one trustee loses their key, you must:
- Cut the padlock
- Manufacture a new lock
- Issue three new keys
- Move everything to the new lock
This is traditional key rotation. It requires moving assets. It is expensive, risky, and operationally painful.
Now imagine a padlock that can rekey itself while remaining closed. The trustees insert their old keys. The lock internally scrambles its mechanism. Each trustee receives a new key that fits the same lock.
The warehouse door never opens. Nothing moves. But the old keys are now worthless. This is a key refresh.
How Leading Platforms Handle Key Refresh
Let us examine how actual custody providers implement these capabilities, because the difference between marketing claims and operational reality is significant.
Take Fireblocks: MPC Refreshing in Production
Fireblocks provides a clear example of how key refresh works in a real-world MPC custody platform. Their architecture uses a 3-of-3 MPC scheme where:
- One key share lives on the customer’s hardware, such as a mobile app or server
- Two key shares reside in Fireblocks’ SGX-secured cloud environments
How Their Refresh Mechanism Works
When a user loses access to their mobile device due to damage, loss, or biometric changes, they do not need to move funds to a new wallet. Instead, they use a recovery passphrase established during onboarding to regenerate their mobile key share.
Take a real scenario. A compliance officer drops their phone in a taxi. With traditional custody, this triggers a multi-day operational nightmare involving generating new wallets, moving funds, and updating records.
With Fireblocks’ architecture:
- The user downloads the Fireblocks mobile app on their new device
- They enter their recovery passphrase
- The system regenerates its specific key shard
The underlying wallet address never changes. Assets never move. The compromised shard on the lost phone is rendered unusable.
This is a key refresh through shard regeneration. The platform does not rotate the entire key. It refreshes individual shards while maintaining the same master key. The assets remain in place. Security improves.
Fireblocks also offers a Verify Passphrase feature that allows users to confirm their recovery passphrase works without executing a recovery. It is similar to testing an emergency evacuation plan without triggering alarms.
The Disaster Recovery Perspective
Fireblocks extends this capability with its Disaster Recovery Kit for enterprise clients.
In a worst-case scenario, such as Fireblocks ceasing operations, customers can reconstruct complete private keys using a combination of:
- An encrypted recovery kit containing the workspace master key
- An RSA private key stored securely by the customer
- The Fireblocks Recovery Tool running on an air-gapped machine
This represents a powerful model of keys without moving assets. Even in a platform shutdown, users recover control without relying on a bankrupt company.
The KIRA Network Approach
For a different architectural approach, consider KIRA Network, which implements recovery through smart contracts rather than MPC shard management.
KIRA’s Recovery Module allows validators to rotate their signing keys if compromise is suspected without losing their staking position or delegations.
Here is how it works:
- Users register a double-hashed recovery secret on-chain
- In an emergency, they present a one-time proof of knowing the original secret
- The protocol reassigns control to a new address
- All modules, including staking, governance, and identity, automatically remap to the new address
The key innovation is that the assets never move. Validator responsibilities, rewards, and delegations transfer seamlessly to the new key. The blockchain handles the rotation natively.
This is especially valuable for institutional validators who cannot afford downtime or slashing events during key rotation.
The Technical Architecture
1. MPC Refreshing Threshold Signature Schemes
In an MPC wallet, the private key never exists in a single form. Instead, it is mathematically distributed as shards across independent nodes.
The Refresh Process
- Each node generates new random entropy
- Nodes communicate via secure channels to re-share the same private key
- The underlying key remains mathematically identical
- Old shards become incompatible with the new signing protocol
Result. Assets stay at the same public address. The blockchain detects no change. An attacker holding an old shard now holds useless data.
2. HSM Key Wrapping Enterprise Hardware
Hardware Security Modules are specialized devices that store keys in tamper-resistant hardware.
The Refresh Process
- The HSM generates a new wrapping key internally
- It decrypts the asset-controlling private key using the old wrapper
- It re-encrypts the same private key with the new wrapper
- The old wrapping key is zeroed from memory
Result. The private key itself remains unchanged. The access mechanism used to retrieve it is replaced. An attacker who extracted encrypted key material cannot decrypt it without the new wrapper.
Limitation. This model depends on trust in the HSM vendor and the physical security of the appliance.
3. Hierarchical Deterministic HD Wallet Migration
This approach is closer to traditional rotation and technically moves assets. However, advanced platforms now make this process nearly invisible.
The system generates a new seed and deterministically derives a fresh set of addresses from it. It then executes controlled internal transactions that migrate assets from the old addresses to the newly derived ones. From the user perspective, the balance appears unified and consistent because the custody layer abstracts the underlying address transition.
The 2026 Innovation
Sweepless migration via smart contract wallets. If assets are held in a smart contract, such as an ERC-4337-based account, ownership can transfer to a new key pair without moving the underlying tokens.
Result. Assets remain in the same contract. The public address appears unchanged. The controlling key is fully replaced.
Why This Matters?
Compromised Insiders
Most breaches are not external hacks. They involve credentials leaving the organization. Former employees, rogue operators, compromised laptops. Key refresh renders stolen shards obsolete on a schedule controlled by the platform.
Quantum Decryption
Quantum-based breakage of RSA or ECC has not materialized yet. However, adversaries are harvesting encrypted material today for future decryption. Regular key refresh ensures captured shards expire before quantum capability becomes practical.
Dormant Backdoors
Backdoors can exist in open-source libraries, dependencies, or supply chain layers. A key generated in 2024 on compromised infrastructure may carry hidden weaknesses. Refreshing keys on the audited infrastructure eliminates this exposure.
Top 5 Crypto Custody Platforms in the USA
We have carefully studied the U.S. custody market and evaluated platforms built for institutional scale. After structured research and security analysis, we found a few crypto custody platforms with clearly differentiated technical models.
1. Anchorage Digital
Anchorage Digital operates as the first federally chartered crypto bank in the U.S., offering qualified custody tailored for institutions. It combines secure key management with staking, governance, and settlement services under a regulated framework.
2. Fidelity Digital Assets
Fidelity Digital Assets provides institutional-grade crypto custody backed by Fidelity’s traditional finance infrastructure. It focuses on cold storage security, operational transparency, and integrated trading services for large investors.
3. Coinbase Custody
Coinbase Custody delivers segregated cold storage designed specifically for institutional clients. It offers insured digital asset storage, compliance reporting, and integration with Coinbase Prime for trading and liquidity access.
4. BitGo
BitGo is one of the earliest institutional crypto custodians in the United States, known for its multi-signature security model and insured cold storage solutions. It serves exchanges, funds, and enterprises with regulated trust structures.
5. Fireblocks
Fireblocks provides MPC-based digital asset custody and secure transfer infrastructure for banks, exchanges, and fintech companies. Its platform enables automated policy controls and high-volume asset movement with institutional-grade security.
Conclusion
Building a crypto custody platform is not a typical software project; treat it as core financial infrastructure. The real cost will reflect the extent to which you implement cryptographic key management and the reliability with which your distributed architecture scales under institutional load. If security is shallow or compliance is an afterthought, the platform may fail under scrutiny, but when engineered correctly, it can securely protect assets and unlock long-term revenue with confidence.
Looking to Develop a Crypto Custody Platform?
At IdeaUsher, we design crypto custody platforms as secure financial infrastructure rather than simple applications. We can architect MPC-based key management, compliance-ready custody workflows, and scalable distributed systems that may withstand institutional audit standards.
With 500,000+ hours of coding experience, our ex-MAANG/FAANG engineers build custody platforms that institutions actually bet their treasuries on.
We handle the parts that keep CTOs up at night:
- MPC key sharding – No single point of failure. Ever.
- AI-driven AML – Block dirty transactions before they’re signed.
- Policy engines – Hardcoded into the signing layer, not bolted on after.
- Staking & RWA support – Turn cold storage into yield-generating infrastructure.
- Off-exchange settlement – Trade without ever depositing on an exchange.
Work with Ex-MAANG developers to build next-gen apps schedule your consultation now
FAQs
A1: A basic MVP could be delivered in around three to four months if the scope is controlled and compliance layers are minimal. However, an enterprise-grade custody system will usually require nine to eighteen months because security audits and regulatory integrations must be implemented with precision.
A2: In most institutional contexts, MPC can offer greater operational flexibility and lower key exposure than traditional multi-signature wallets. Instead of placing full keys on separate devices, it distributes cryptographic shares and collaboratively computes signatures, which may significantly reduce the risk of a single point of compromise.
A3: Custody platforms should not rely solely on asset storage fees to scale sustainably. They can integrate staking services and institutional transaction processing, which may generate recurring yield and spread-based income.
A4: In most jurisdictions, custody providers will need regulatory authorization because they safeguard client assets and may perform financial activities. The specific license structure depends on local digital asset laws and whether the platform handles fiat rails or offers staking services.