Managing the complexities of international travel requires an uncompromising commitment to visa app security, as these digital systems handle sensitive biometrics, financial records, and official government documentation. Providing users with peace of mind throughout every stage from the initial document upload to final status tracking is the only way to establish trust and ensure compliance.
The visa app necessitates a multi-layered defense strategy that integrates data encryption, identity verification, and proactive threat monitoring into a seamless daily workflow. The ultimate effectiveness of these safeguards depends on their ability to neutralize real-world risks, such as unauthorized access or integration vulnerabilities, without ever compromising the platform’s essential usability.
In this blog, we explain how to ensure security in visa apps like Atlys by breaking down core security measures, architectural considerations, and practical steps involved in building a secure and compliant visa processing platform.
Why Security Is Critical in Visa Apps Today?
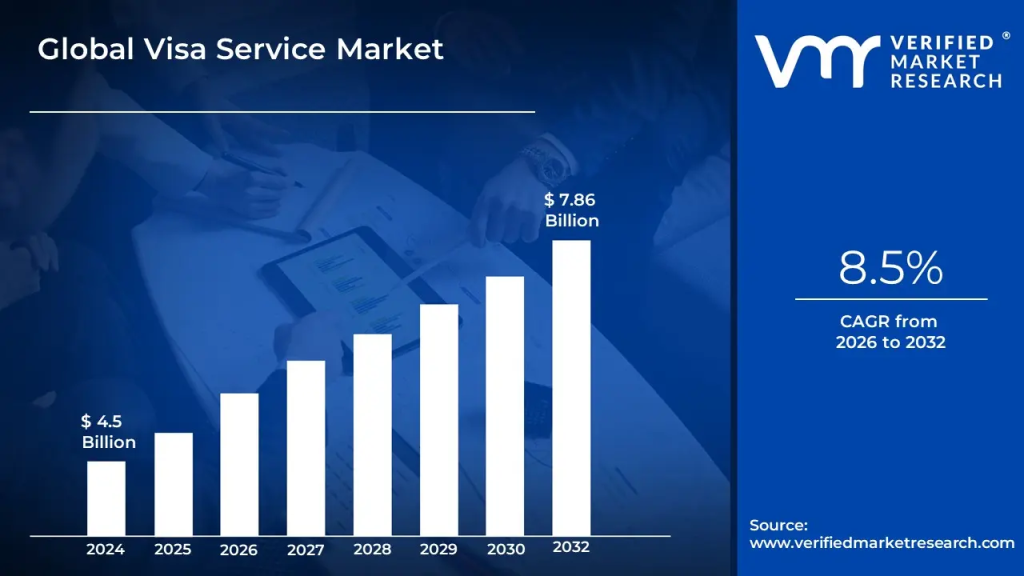
The visa service market size was valued at USD 4.5 billion in 2024 and is projected to reach USD 7.86 billion by 2032, growing at a CAGR of 8.5% during the forecast period 2026 to 2032. As this market expands, implementing robust security frameworks becomes the primary differentiator for platforms aiming to protect high-stakes traveler data.
Data is often compared to oil, but for a visa platform it is more like “nuclear material”, highly valuable yet dangerous if mishandled. The global average cost of a data breach reached $4.88 million in 2024, a 10% increase from the previous year. Also, the Global deepfake fraud skyrocketed by 700% in Q1 2025 alone, with synthetic identity document fraud jumping by 378%
A. Sensitive Data Risks in Visa Processing Apps
Visa applications require full-spectrum identity data such as passport scans, National IDs, biometric “selfie” checks, and bank statements, making it a prime target for identity theft and fraud.
The risk of mishandling the data during OCR (Optical Character Recognition) or improper cloud storage can cause data exposure. For platforms like Atlys, this expands the overall risk surface.
- In-Transit Vulnerabilities: Data being intercepted as it moves from the user’s smartphone to the platform’s backend or to embassy servers.
- Third-Party Leaks: Many visa apps rely on external APIs for document verification or payment. If these hooks are not secured with rigorous mutual TLS (mTLS) protocols, they become the weakest link in your chain.
- Biometric Spoofing: Modern attackers use injection attacks to bypass camera feeds with synthetic images. Without Liveness Detection (iBeta Level 2), your platform could unknowingly process fraudulent applications.
B. Trust as a Growth Driver for Visa Platforms
The Trust Barrier is the biggest friction in travel-tech, where users must share sensitive identity data with unfamiliar platforms. Without institutional-grade visa app security, drop-offs at the document-upload stage limit scalability.
Security acts as a conversion engine. Positioning it as a value proposition shifts a platform from a utility tool to a trusted partner, improving acquisition costs and long-term retention.
| Trust Pillar | Technical Implementation | Growth Impact (ROI) |
| Identity Assurance | Level 2 Liveness Detection & AI-driven document verification. | Increases Conversion: Reduces user hesitation during sensitive document uploads by 40%. |
| Data Sovereignty | Region-specific data residency (GDPR/CCPA compliant) and AES-256 encryption. | Market Expansion: Allows immediate entry into strict regulatory markets like the EU and UK. |
| Institutional Credibility | SOC2 Type II Certification & regular third-party penetration testing. | High-Value Retention: Attracts corporate accounts and high-net-worth individuals who require audited safety. |
| Transaction Security | PCI-DSS Level 1 payment gateways & tokenized financial data. | Reduced Churn: Eliminates payment friction and chargeback risks, stabilizing monthly recurring revenue. |
C. Real Consequences of Security Failures
The fallout from a security breach in the visa space is multi-dimensional and often terminal for a startup. From a financial perspective, the average cost of a data breach has climbed past $4.4 million, but for a fintech/travel-tech hybrid, the hidden costs are even higher.
- Legal and Regulatory Hammers: Non-compliance with international data laws can lead to fines up to 4% of global annual turnover and loss of “Trusted Partner” status, potentially shutting down operations.
- Reputational Bankruptcy: If a visa app is linked to identity theft, the brand is effectively dead. Recovery is difficult since travel is personal and high-stress.
- Blocklisting by Government Entities: Embassies may block platforms submitting compromised or poorly verified data, banning IP ranges or API keys and collapsing the entire service pipeline.
How Visa Apps Like Atlys Handle User Data?
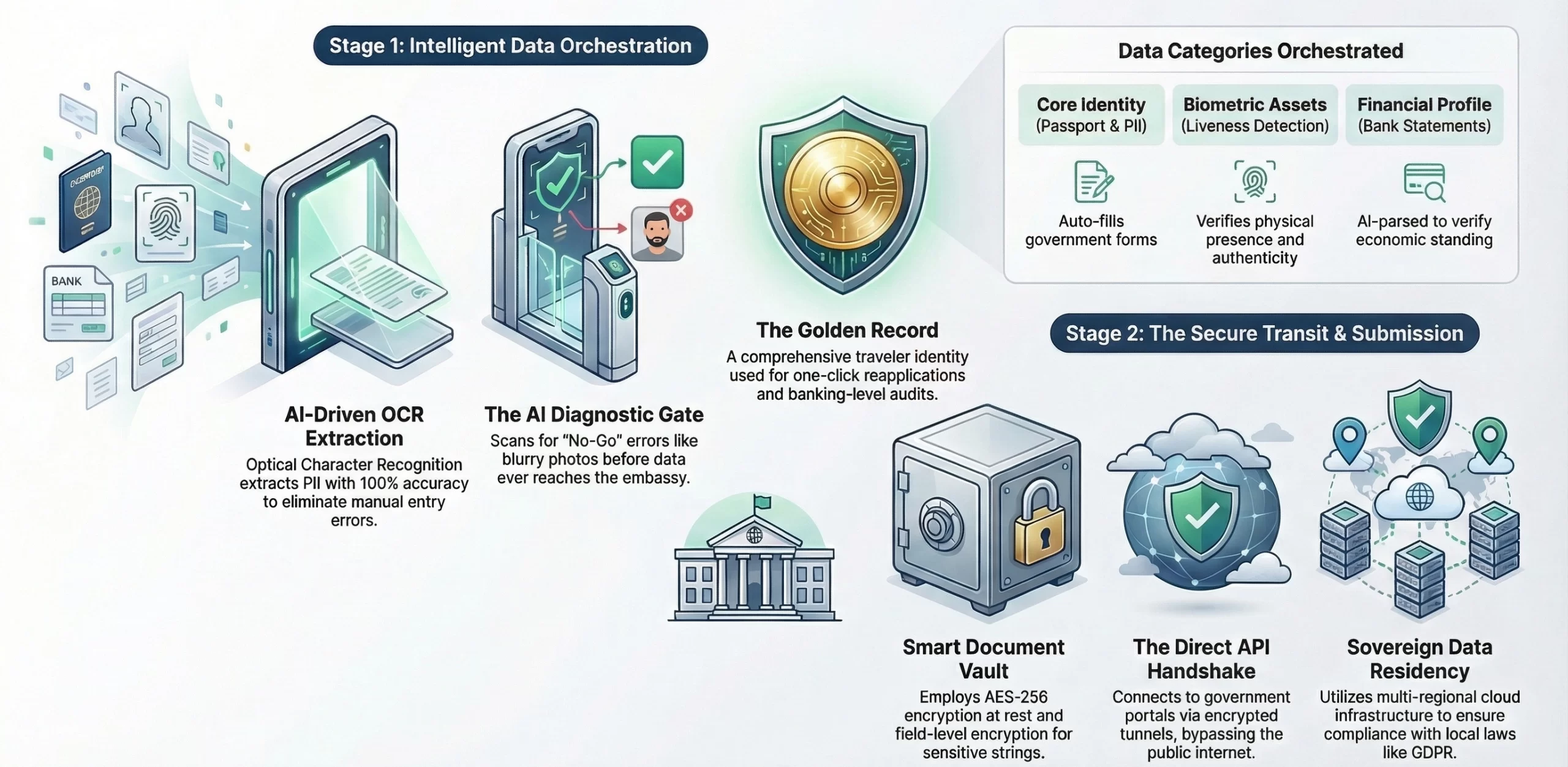
Modern visa platforms act as high-orchestration engines between user input and government systems. With Pre-Check and Vault architecture, data is cleaned, AI-validated, and stored in Ready-Retrievability for one-click reapplications with 99% accuracy.
The goal is to build a Golden Record for each traveler, comprehensive for e-visa portals and secure enough for banking-level audits, reducing repetitive friction in international travel.
A. Types of Data Collected in Visa Apps
Platforms like Atlys curate a Global Travel Identity by collecting diverse data for fast processing. Consequently, this follows Data Minimization by capturing only the specific information that immigration authorities require for successful applications.
The following table categorizes the Hard Identity and Supportive Evidence required to move an application from a smartphone to an embassy’s approval queue:
| Data Category | Specific Data Points | Purpose & Technical Utility |
| Core Identity (PII) | Full Name, DOB, Nationality, Passport Number, Gender. | Extracted via OCR (Optical Character Recognition) to auto-fill government forms with 100% accuracy. |
| Biometric Assets | High-resolution selfies, Passport bio-page scans. | Used for Face Matching and “Liveness Detection” to verify the user is physically present and authentic. |
| Financial Profile | Bank statements (3-6 months), Income certificates, Tax returns. | Parsed by AI to verify “Economic Standing,” a primary factor in preventing visa rejections for many Western nations. |
| Travel & Social History | Past visa stamps, Rejection history, Family details, Employment status. | Feeds the Predictive Rejection Engine to calculate the probability of approval before the user pays. |
| Transactional Data | Credit/Debit card tokens, Billing address, Currency preferences. | Handled via PCI-DSS Level 1 gateways; allows for automated “Exchange Rate Refunds” if government fees fluctuate. |
B. Where and How User Data Is Stored
The “Where” of data storage is a matter of legal jurisdiction and sovereignty. Top-tier platforms utilize Multi-Regional Cloud Infrastructure (such as AWS or Google Cloud) with Data Residency logic. This ensures that if a German citizen uses the app, their data stays on servers within the EU to comply with GDPR.
The “How” involves a layered defense strategy known as a Smart Document Vault:
- Encryption at Rest: The system encrypts every document using AES-256 (military-grade) protocols before it touches the disk.
- Field-Level Encryption: Additionally, the architecture encrypts sensitive strings (like Passport Numbers) individually. This ensures that even if an attacker partially compromises a database table, the actual identity markers remain unreadable.
- Tokenization: Furthermore, the platform replaces financial data with non-sensitive tokens for internal processing. This ensures the system only exposes raw data during the final submission to the government.
C. Data Flow From User to Embassy Systems
The journey of a document from a user’s camera to an embassy’s database is the most vulnerable part of the lifecycle. Professional-grade platforms secure this data transit through Mutual TLS (mTLS), a protocol where both the app and the server must authenticate each other before a single byte is exchanged.
The process typically follows a three-stage “Bridge” logic:
- The Validation Gate: Before hitting the embassy, the data is scanned by an AI Diagnostic engine. This identifies “No-Go” errors (like a blurry photo or an expired passport) that would trigger an automatic government rejection.
- The API Handshake: For e-visa-ready countries, the app connects directly to the government’s API. This is a secure, encrypted tunnel that bypasses the public internet.
- The Submission Audit: After the user hands over the data, the app maintains an immutable audit log. This records exactly what the system sent and when, providing a legal paper trail that is essential for dispute resolution and maintaining the platform’s allowlisted status with foreign consulates.

Core Security Layers in Visa App Development
Building a visa platform like Atlys requires a defense-in-depth strategy, where security is not a single “gate” but multiple interlocking layers across frontend, backend, and infrastructure to prevent total system failure.
The following table outlines these layers of visa app security, defining technical requirements and rationale to meet global security benchmarks and ensure scalable, secure visa processing.
| Security Layer | Technical Implementations | Strategic Rationale & Application |
| Frontend Security | SSL/TLS 1.3 Pinning, Device Fingerprinting, and Root/Jailbreak Detection. | Protects user sessions from man-in-the-middle attacks and prevents unauthorized devices from accessing the app. |
| Backend Security | AES-256 Field-Level Encryption, Role-Based Access Control (RBAC), and Salted Hashing. | Secures stored identity markers so that even internal database admins cannot view raw passport data. |
| Cloud Infrastructure | Virtual Private Cloud (VPC), WAF (Web Application Firewall), and Intrusion Detection Systems (IDS). | Ensures regional data residency compliance (GDPR/CCPA) and mitigates large-scale DDoS attacks automatically. |
| API & Integrations | Mutual TLS (mTLS), OAuth 2.0 with Scopes, and Strict Payload Validation. | Secures embassy connections and third-party hooks, preventing malicious code injection during the data handoff. |
Must-Have Security Features in Visa Apps
Security features are not just add-ons but core to a visa platform’s value. Platforms like Atlys automate the “Trust Chain” through essential modules that protect user identity and ensure legal compliance.
These features represent the difference between a scalable global enterprise and a significant liability.
1. End-to-End Data Encryption Standards
To protect sovereign identity markers, the application must employ a zero-visibility architecture where data remains unreadable to unauthorized parties from the moment of capture.
- Perfect Forward Secrecy (PFS): By utilizing ephemeral session keys, the platform ensures that even if an attacker compromises a long-term private key in the future, past communication remains encrypted and secure.
- AES-256 at Rest: The system stores all passport scans and biometric files using military-grade Advanced Encryption Standard. This renders the data useless to any intruder who manages to bypass outer perimeter defenses.
- TLS 1.3 in Transit: Utilizing the latest transport layer security protocols prevents “Man-in-the-Middle” attacks, ensuring a secure tunnel exists between the traveler’s smartphone and your backend infrastructure.
2. Secure Document Upload and Storage
Handling high-resolution passport images requires a specialized sandboxed ingestion process to prevent malicious files from entering your cloud environment.
- Malware & Steganography Scanning: The system routes every uploaded PDF or JPEG through an isolated quarantine zone. Here, AI scanners check for embedded scripts or hidden code before the platform moves the file to permanent storage.
- Object-Level Locking: By implementing “Write Once, Read Many” (WORM) policies, the platform prevents accidental or malicious deletion of critical visa documents, ensuring an immutable audit trail for embassy verification.
- S3 Managed Key Encryption: Utilizing cloud-native Key Management Services (KMS) ensures the system rotates encryption keys frequently and stores them in hardware security modules (HSMs) separate from the data itself.
3. Multi-Factor Authentication (MFA)
Password-based security is an obsolete standard for platforms handling government-grade identity; a multi-layered verification approach is essential to prevent account takeovers.
- Adaptive Risk-Based MFA: The system monitors login context, such as IP reputation and geographic velocity, triggering secondary challenges only when an anomaly is detected to maintain a low-friction user experience.
- TOTP & Biometric Push: Moving beyond insecure SMS codes, the platform utilizes Time-based One-Time Passwords or encrypted mobile push notifications to verify the user’s physical possession of their device.
- Secure Enclave Integration: Leveraging the hardware-level security of modern smartphones ensures that biometric data never leaves the user’s device, maintaining privacy while providing ironclad authentication.
4. Role-Based Access Control (RBAC)
Internal security is a critical pillar of compliance; RBAC ensures that your staff only sees the data absolutely necessary for their specific job function.
- Principle of Least Privilege (PoLP): Engineers, customer support agents, and marketing teams are granted granular permissions, preventing any single internal account from having “God-Mode” access to the entire database.
- Just-In-Time (JIT) Access: For high-sensitivity tasks, administrative access is granted only for a limited window, reducing the standing risk of privileged accounts being targeted by attackers.
- Immutable Access Logs: Every internal interaction with user data is recorded in a tamper-proof log, providing the paper trail required for SOC2 and ISO 27001 certifications.
5. Real-Time Fraud Detection Systems
Protecting your platform’s reputation with foreign consulates requires proactive defense against visa farming and automated bot attacks.
- Behavioral Biometrics: The AI engine analyzes interaction patterns such as typing rhythm and cursor movement to distinguish between a genuine traveler and a scripted bot trying to mass-submit applications.
- Device Fingerprinting: By identifying the unique hardware signature of a device, the system can block device farms that attempt to run hundreds of fraudulent applications from a single physical location.
- Velocity & IP Geofencing: Real-time monitoring flags accounts that attempt to log in from high-risk jurisdictions or multiple countries in a short timeframe, preventing large-scale credential stuffing attacks.
6. Secure Payment Gateway Integration
Decoupling the visa app from raw credit card information ensures total financial security.
- PCI-DSS Level 1 Tokenization: The app sends sensitive card data directly to a certified processor like Stripe or Adyen. The processor returns a token for the transaction, ensuring you never store the actual card number.
- 3D Secure 2.0 Implementation: This protocol provides an extra layer of authentication for online payments, significantly reducing the risk of fraudulent chargebacks and ensuring the platform remains in good standing with banks.
- Automated Reconciliation: The system matches every payment token to a specific visa application ID, ensuring financial transparency and making the platform audit-ready for future investment rounds.
Compliance Standards Visa Apps Must Follow
Regulatory compliance is the License to Operate in visa tech. Being compliant is a continuous commitment to global laws, and failure can lead to fines or loss of access to government API gateways.
The following table outlines the critical regulatory pillars that a high-growth visa app like Atlys must master to ensure global scalability and investor-grade risk management.
| Compliance Pillar | Regulatory Framework | Strategic Rationale & Implementation |
| Data Privacy | GDPR (EU), CCPA (US), & DPDP (India). | Mandates “Right to be Forgotten” and strict data residency. Ensures users have total control over their sovereign identity data. |
| Security Audits | ISO 27001 & SOC2 Type II. | Provides third-party validation of internal security controls. Essential for “Enterprise-Level” trust and securing institutional funding. |
| Identity Integrity | KYC (Know Your Customer) & AML (Anti-Money Laundering). | Prevents identity fraud and ensures the platform is not used for illicit financial movement or human trafficking. |
| Sovereign Mandates | Country-Specific Data Localization. | Requires physical servers within specific borders (e.g., Vietnam or Russia) to process local citizen data legally. |

Common Security Mistakes in Visa App Development
Visa apps often face risks like weak authentication, poor encryption, and insecure APIs, exposing sensitive data. Our developers address these with strong security measures, advanced encryption, and regular testing for safe, reliable apps.
1. Weak Encryption and Poor Key Management
Challenge: Storing sensitive passport numbers or biometric data using outdated algorithms or hard-coded keys makes the database an easy target.
Solution: Our developers implement AES-256 Field-Level Encryption and utilize Cloud Key Management Systems (KMS). This ensures that even with database access, the sensitive PII remains cryptographically unreadable without rotating, hardware-secured keys.
2. Insecure API Integrations
Challenge: Exposing internal embassy endpoints or using unauthenticated webhooks allows malicious actors to intercept data or inject fraudulent visa applications.
Solution: We architect Mutual TLS (mTLS) and OAuth 2.0 Scopes. Our engineers ensure every API handshake is bidirectional and verified, creating a “Hardened Bridge” that prevents unauthorized traffic from hitting government portals.
3. Lack of Regular Security Audits
Challenge: Relying on initial security setups without addressing “Zero-Day” vulnerabilities leads to stagnant defenses that cannot withstand modern, evolving cyber-attacks.
Solution: Our team integrates Automated DevSecOps Pipelines. By running continuous vulnerability scans and scheduling quarterly third-party penetration tests, our developers identify and patch security blind spots before hackers can exploit them.
4. Ignoring User Session Management Risks
Challenge: Persistent sessions or weak token expiration on shared devices can allow unauthorized users to access and modify private visa documents.
Solution: We deploy Short-Lived JWT Tokens and Biometric Re-Authentication. Our developers implement inactivity timeouts and device-fingerprinting, ensuring the system instantly terminates a session if it detects suspicious or unauthorized access patterns.
Secure Architecture for Visa Apps Like Atlys
Secure architecture in visa apps focuses on protecting user data, ensuring system reliability, and maintaining compliance with global standards. It combines encryption, access controls, and secure APIs to deliver safe and seamless user experiences.
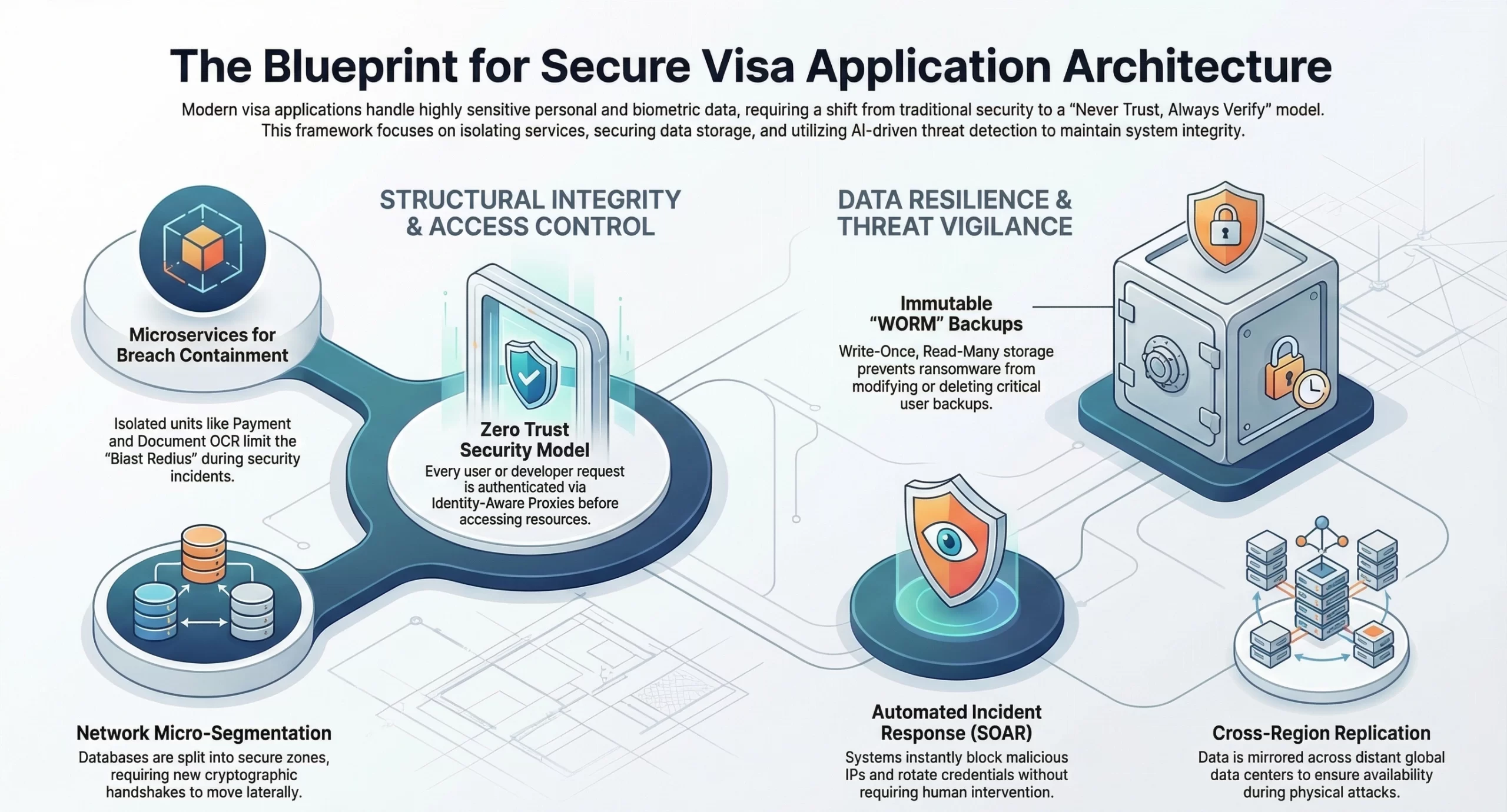
1. Microservices vs Monolithic Architecture
In the visa processing sector, the choice of architecture directly impacts the platform’s blast radius during a security incident.
- Service Isolation: A microservices architecture splits the app into units like Payment Service, Document OCR Service, and Embassy API Gateway. If one is breached, there is no direct access to the Document Vault.
- Independent Scalability: The Document Parsing service can scale across cloud zones during peak seasons, preventing performance drops, security timeouts, and race condition vulnerabilities.
- Granular Security Policies: Each service has its own firewall and security group, enabling “Least Privilege” so services like Payment cannot access the Biometric database.
2. Zero Trust Security Model Implementation
The traditional “Castle and Moat” security model is obsolete in 2026; modern visa apps must operate on the principle of “Never Trust, Always Verify.”
- Identity-Aware Proxy (IAP): Every request from users or developers is authenticated and authorized using encrypted JWT tokens before accessing backend resources.
- Micro-Segmentation: Networks are split into secure zones, requiring a new cryptographic handshake to move between databases like User Profile and Passport, preventing lateral movement.
- Continuous Validation: Sessions are constantly checked, and changes in device Fingerprint or IP trigger termination and MFA alerts.
3. Secure Data Storage and Backup Systems
Data is the lifeblood of the visa business, and its permanent availability is a non-negotiable requirement for maintaining government Trusted Partner status.
- Cross-Region Replication (CRR): User data is mirrored across distant data centers like US-East and EU-West, preventing loss during outages or physical attacks.
- Immutable Backups: Using WORM (Write Once, Read Many) storage, backups cannot be modified or deleted, even by a “Root” administrator, protecting against ransomware.
- Hardware Security Modules (HSM): Encryption keys are stored in tamper-evident hardware and never exist in plain text, making them highly resistant to software-based attacks.
4. Monitoring and Threat Detection Systems
A professional visa app must maintain a 24/7 watchtower capability to identify and neutralize emerging threats before they escalate into breaches.
- SIEM Integration (Security Information and Event Management): Aggregates billions of logs into a centralized AI system to detect Low and Slow attack patterns missed by humans.
- Real-Time Anomaly Detection: ML models set a baseline for behavior. Deviations like unusual passport export activity trigger an “Emergency Lockdown”.
- Automated Incident Response (SOAR): Detects threats like SQL injection and instantly blocks IPs while rotating database credentials without human intervention.

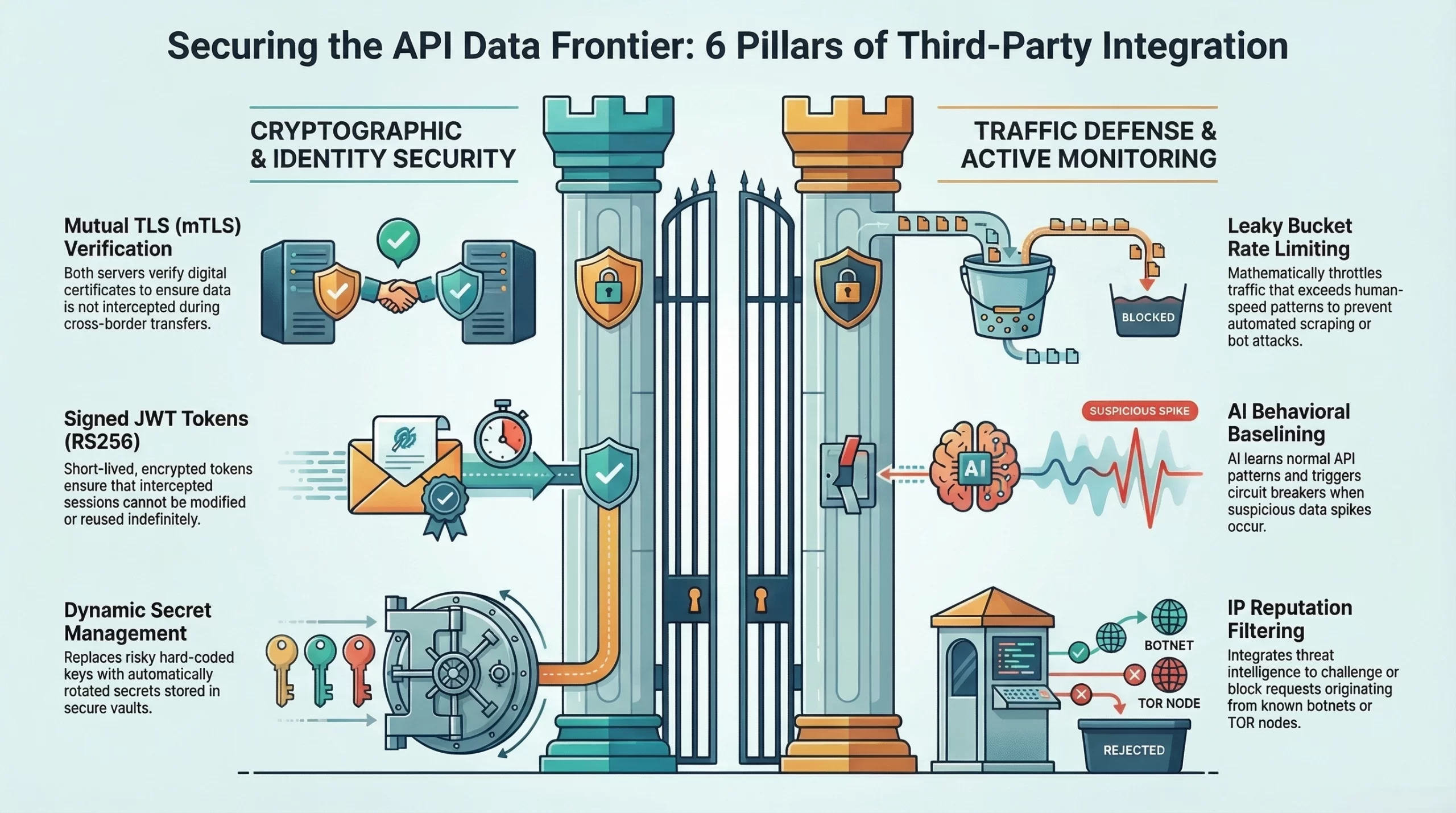
How to Secure Third-Party API Integrations?
Visa app security depends on the weakest link. Platforms like Atlys act as middleware, making APIs the Data Frontier. Unsecured APIs risk data exfiltration, requiring a strong cryptographic handshake architecture beyond passwords.
1. Embassy and Government API Risks
Interfacing with government systems presents a unique set of security challenges, as these legacy portals often lack the modern defenses of private-sector APIs.
- Legacy Protocol Vulnerabilities: Older SOAP and early REST systems may face XML injection or replay attacks. Middleware must act as a sanitization layer to clean all data.
- Man-in-the-Middle (MITM) Interception: Cross-border data risks interception. mTLS (Mutual TLS) ensures both servers verify digital certificates.
- Credential Exposure: Hard-coded API keys are risky. Use dynamic secret management like HashiCorp Vault with automatic rotation and no plain text storage.
2. Secure Token-Based Authentication
To maintain a stateless and secure environment, the platform must replace permanent credentials with short-lived, encrypted tokens.
- JWT (JSON Web Tokens) with RS256: Instead of simple strings, we use tokens signed with private/public key pairs. This ensures that even if an attacker intercepts a token, they cannot modify it without breaking the cryptographic signature.
- Short-Lived Access Tokens: By setting token expiration windows to minutes rather than hours, the platform minimizes the window of opportunity for an attacker to use a stolen session.
- Refresh Token Rotation: Every time a new access token is requested, the old “Refresh Token” is invalidated. This single-use logic ensures that if a breach occurs, the attacker is instantly locked out the moment the user’s session refreshes.
3. Rate Limiting and Abuse Prevention
A common attack vector for visa platforms is scraping or credential stuffing, where bots attempt to guess passport numbers or visa statuses by hitting APIs thousands of times per second.
- Leaky Bucket Algorithms: We implement sophisticated rate-limiting that allows for natural bursts of user activity while mathematically throttling any traffic that exceeds human-speed patterns.
- IP Reputation Filtering: The API gateway is integrated with global threat intelligence feeds. If a request originates from a known “Tor Exit Node” or a data center associated with botnet activity, the request is challenged with a “Hard CAPTCHA” or blocked entirely.
- Payload Size Constraints: By strictly limiting the size of incoming API requests, the platform prevents buffer overflow attacks where an attacker tries to crash the server by sending massive amounts of junk data disguised as a passport scan.
4. Continuous API Monitoring Strategies
Security is not a “Set and Forget” configuration; it requires real-time visibility into every byte moving across your integration points.
- API Behavioral Baselining: AI learns normal embassy API patterns. Sudden spikes like 2KB to 2MB trigger an automatic circuit breaker to prevent data leaks.
- Shadow API Discovery: Automated scanners detect “Zombie” or “Test” APIs left open, common entry points for attackers.
- Real-Time Log Aggregation: The system logs every API call and response without PII in an immutable trail, enabling rapid forensic reconstruction of suspicious events.
Cost of Building a Secure Visa App
Building a secure visa app requires a risk-adjusted investment, with significant focus on a strong security backbone rather than just features and UI/UX. Early investment in encryption and compliance prevents costly technical debt and ensures long-term scalability and reliability.
A. Security Cost vs Development Cost Breakdown
The visa app security costs rise to 25–30% of the budget, compared to 10–15% in typical apps. This premium covers critical features like biometric checks, secure key management, and multi-region data handling.
- Encryption & Vaulting: Developing the secure document vault is a high-cost phase, as it involves integrating Hardware Security Modules (HSMs) and field-level encryption that doesn’t degrade system performance.
- Biometric Integration: Implementing iBeta Level 2 certified liveness detection is significantly more costly than standard camera APIs, as it requires specialized third-party licensing and rigorous spoof-testing.
- Architecture Complexity: Building a Zero-Trust microservices environment requires more senior DevSecOps engineers than a standard monolithic build, increasing the hourly development rate but ensuring superior long-term resilience.
B. Cost of Compliance and Certifications
Compliance is a recurring fixed cost that acts as the platform’s legal insurance policy. For a startup looking to scale globally, these certifications are the “Gold Seals” that institutional investors look for during due diligence.
- Audit Fees: Obtaining a SOC2 Type II or ISO 27001 certification involves hiring external auditors to perform a deep-dive into your company’s internal processes. These audits can cost anywhere from $20,000 to $50,000 annually.
- Legal Counsel: Navigating the data sovereignty laws of different nations (like the DPDP in India or GDPR in the EU) requires specialized legal consultants to draft ironclad privacy frameworks and data-sharing agreements.
- Penetration Testing: High-stakes platforms must conduct “Black-Box” and “White-Box” penetration testing at least twice a year. Hiring elite ethical hackers to find vulnerabilities is an essential investment to prevent multi-million dollar breaches.
C. Long-Term Cost of Security Maintenance
Security is not a one-time purchase; it is an ongoing operational expense (OPEX). As cyber threats evolve, particularly with the rise of AI-driven fraud, the platform’s defenses must be constantly updated.
- Security Operations Center (SOC): Whether handled in-house or outsourced (MDR), 24/7 monitoring of system logs and threat detection is a mandatory cost to ensure immediate response to anomalies.
- Key Rotation & Patching: The administrative overhead of managing encryption keys, rotating secrets, and applying zero-day patches across a microservices architecture requires dedicated DevSecOps hours.
- AI Model Retraining: To stay ahead of sophisticated deepfakes, the platform’s fraud detection AI must be periodically retrained with new datasets, representing a continuous R&D cost that ensures the platform remains future-proof.
Security Investment & Development Cost
The security investment & development cost outlines the critical financial and technical roadmap for building a high-assurance visa platform, balancing robust Zero-Trust infrastructure costs with long-term global scalability.
| Development Phase | MVP – Mid-Scale | Enterprise | What Is Being Built |
| Core Architecture | $35,000 – $55,000 | $85,000 – $120,000 | Microservices framework with Zero-Trust identity protocols and VPC isolation. |
| Identity & Biometrics | $20,000 – $30,000 | $50,000 – $75,000 | Liveness detection engines and AI-driven OCR for 150+ passport types. |
| Data Vault & Encryption | $15,000 – $25,000 | $40,000 – $60,000 | AES-256 field-level encryption with HSM-based key management systems. |
| Compliance & Audits | $10,000 – $20,000 | $35,000 – $55,000 | SOC2/ISO setup, legal framework mapping, and initial VAPT testing. |
| Fraud & Monitoring | $12,000 – $18,000 | $30,000 – $50,000 | Real-time SIEM integration and behavioral anomaly detection engines. |
| Total Estimated Total | $92,000 – $148,000 | $240,000 – $360,000 | Comprehensive digital fortress ready for global visa processing. |
How IdeaUsher Ensures Visa App Security?
We have worked with numerous enterprises building and launching their app and using that expertise, our ex-FAANG/MAANG developers bring 500,000+ hours of expertise to build AI-driven platforms. Security is embedded into our core architecture, ensuring compliance with global data protection standards in 2026.
A. Our Security-First Development Framework
Our engineers implement DevSecOps protocols, integrating automated security scanning into every stage of the CI/CD pipeline. This proactive approach identifies vulnerabilities early, ensuring your platform’s code is hardened against sophisticated SQL injections and cross-site scripting.
B. Compliance Expertise Across Global Markets
We navigate complex international regulations including GDPR, HIPAA, and PCI-DSS Level 1 requirements. Our team ensures your visa application meets specific regional data residency laws, utilizing localized cloud hosting to maintain strict legal compliance.
C. Real Projects We’ve Secured
Leveraging our extensive portfolio, we have successfully deployed various platforms like Carpooll, GetOn Scooters, Albportal, etc. that manage millions of sensitive documents. Our experience includes building encrypted vaults and biometric verification systems that currently protect global applicant data from breaches.
D. How We Handle Sensitive User Data
We utilize AES-256 encryption and hardware security modules to safeguard PII at rest and in transit. By implementing zero-knowledge architecture, we ensure that sensitive passport and financial data remains accessible only to authorized personnel.

Key Questions to Ask Before Hiring Developers
The technical team is the most critical asset in the visa app venture. Building a platform like Atlys is not a standard project but a high-stakes security challenge, requiring developers with a “Security-First” DNA over speed or UI focus.
A. What Security Standards Do You Follow?
A developer’s answer to this question reveals whether they understand the institutional-grade requirements of the travel-tech sector.
- Framework Alignment: The team should be able to articulate their adherence to OWASP Top 10 for web security and ASVS (Application Security Verification Standard) for mobile apps.
- Certification Readiness: Ask if they have experience building audit-ready systems. If they haven’t worked within the constraints of SOC2 Type II or ISO 27001, your platform may fail its first major institutional due diligence.
- Cryptographic Mastery: They should specify the use of AES-256 for data at rest and TLS 1.3 for data in transit, along with a clear strategy for managing encryption keys using hardware-backed security.
B. How Do You Handle Sensitive User Data?
The handling of passport scans and biometrics is the “Litmus Test” for any development team in this space.
- Data Minimization & Isolation: A professional team will implement Field-Level Encryption, ensuring that even if a database table is breached, the actual passport numbers and names remain unreadable.
- The “Zero-Knowledge” Philosophy: Inquire if they can build an architecture where your own internal employees cannot view a user’s sensitive documents unless specifically authorized through a Just-In-Time (JIT) access request.
- Secure Ingestion: They must explain how they sanitize uploaded files to prevent Malware Injection attacks, where a hacker hides a malicious script inside a seemingly harmless visa photo.
C. Can You Ensure Compliance Across Regions?
Visa apps are inherently global, meaning your developers must be regulatory architects who understand that code has borders.
- Dynamic Data Residency: Can they implement Geo-Sharding? For example, ensuring that an Indian citizen’s data never leaves servers in Mumbai, while an EU citizen’s data remains in Frankfurt to satisfy GDPR mandates.
- Localized Legal Hooks: The team should be able to integrate country-specific consent managers that adapt the UI based on the user’s IP address, ensuring you are legally compliant in every market you enter.
- Sovereign API Expertise: Ask about their experience interfacing with government e-visa portals. These integrations require a deep understanding of mTLS (Mutual TLS) and specific government-grade authentication protocols.
D. What Is Your Approach to Risk Mitigation?
A high-level developer doesn’t just build features; they build “Failure Modes” and “Recovery Engines.”
- Automated Threat Detection: The team should propose an AI-driven SIEM (Security Information and Event Management) system that identifies Brute Force or DDoS attacks in real-time and triggers an automatic lockout.
- The “Circuit Breaker” Logic: In the event of an embassy API breach or a suspicious surge in data exports, the system should be designed to self-isolate, cutting off the affected service to prevent a platform-wide compromise.
- Disaster Recovery (DR) RPO/RTO: They must provide a clear “Recovery Point Objective.” If a server goes down, how many minutes of data will you lose, and how many seconds will it take for the “Failover” system to bring the platform back online?
Future Trends in Visa App Security
As the global economy becomes more AI-driven, visa platforms must evolve to counter synthetic identity threats and advanced cyber risks. Future apps like Atlys will move toward Sovereign Identity Nodes, enhancing user control while strengthening trust equity through secure, automated verification.
1. Blockchain for Identity Verification
Blockchain technology is poised to solve the “Single Point of Failure” problem that plagues traditional centralized databases.
- Self-Sovereign Identity (SSI): Using decentralized identifiers (DIDs), users store data in a digital wallet and share only “Cryptographic Proof”, reducing data exposure and liability.
- Immutable Audit Trails: All interactions are recorded on a private ledger, creating a tamper-proof history that prevents fraudulent record insertion.
- Zero-Knowledge Proofs (ZKP): Verifies conditions like “over 18” or “$5,000 balance” without revealing actual personal data.
2. Biometric Authentication in Travel Apps
The future of travel-tech lies in touchless security, where a user’s physical self becomes their primary, unhackable credential.
- Multimodal Biometrics: Combines voice print and iris recognition with face scans to create a 360-degree identity, making deepfake bypass nearly impossible.
- Behavioral Biometric Continuous Auth: Monitors user behavior and interaction signature during sessions, triggering re-authentication if patterns change.
- On-Device Secure Enclave Processing: Sensitive face maps stay on-device, with processing in secure hardware so no biometric data reaches the cloud.
3. AI-Driven Security Automation
As cyberattacks become faster and more automated, the defense systems of visa platforms must move at machine speed to neutralize threats before they can cause damage.
- Self-Healing Infrastructure: AI-driven DevSecOps detects and patches Zero-Day vulnerabilities, updating firewall rules in milliseconds to block new threats.
- Predictive Threat Hunting: AI hunters simulate attack scenarios in a constant warfare model to stay ahead of advanced hackers.
- Automated Fraud Graphing: AI identifies clusters of fraudulent activity across regions, stopping visa-farming operations before submission.
Conclusion
Visa app security plays a critical role in protecting sensitive user data and maintaining trust. Apps like Atlys must prioritize advanced encryption, secure authentication, and strict compliance with global data protection standards. Continuous monitoring, regular security audits, and safe API integrations help prevent potential threats and vulnerabilities. Emphasizing user privacy and transparent data handling further strengthens credibility. A secure visa application platform not only safeguards information but also delivers a smooth, reliable experience, encouraging users to confidently manage their travel needs in a fast-growing digital environment.
Why Choose IdeaUsher for Secure Visa Application Development?
Building a visa application platform like Atlys demands an uncompromising approach to security, where sensitive personal data, passport scans, and government interactions must be protected against evolving cyber threats while maintaining regulatory compliance.
We build AI-driven products across industries, specializing in performance systems, model integration, and scalable infrastructure. Our expertise helps us create visa automation apps that balance ironclad security, seamless user experiences, and long-term trust sustainability.
Our ex-FAANG and MAANG engineers bring over 500,000+ hours of hands-on AI development experience, allowing us to architect security-first travel platforms aligned with data protection regulations, encryption standards, and zero-trust architectures.
Why Hire Us:
- Security & Compliance Expertise: We build high-assurance ecosystems with end-to-end encryption, multi-factor authentication, and intrusion detection, handling sensitive PII and government documents across jurisdictions.
- Custom Identity Protection: We develop data masking, secure storage with automated expiration, and audit-ready compliance frameworks to strengthen user trust and regulatory readiness.
- Full-Cycle Ownership: We manage infrastructure, SOC 2, GDPR/CCPA, and secure architectures to deliver a threat-resilient, market-ready visa app.
Work with Ex-MAANG developers to build next-gen apps schedule your consultation now
FAQs
A.1. Visa apps must employ AES 256 encryption for data at rest and TLS 1.3 for data in transit. This ensures that sensitive personal identifiable information, such as passport numbers and biometric scans, remains unreadable to unauthorized parties during storage and transmission.
A.2. Liveness detection uses AI to verify that a real person is present during a selfie scan, preventing the use of static photos or deepfakes. This biometric “bind” ensures that the applicant is the rightful owner of the uploaded travel documents.
A.3. Compliance with SOC2 and GDPR demonstrates that the platform adheres to strict global standards for data privacy and operational security. For entrepreneurs, this builds essential trust with users and government authorities, reducing the legal risks associated with handling international traveler data.
A.4. A Secure Visa Vault is an encrypted sandbox where users store documents for reuse. By utilizing role based access controls, the system ensures that only necessary microservices can access specific data points, minimizing the exposure of sensitive files during the application process.