The federal marketplace is a high-yield frontier for SaaS innovators, yet it remains protected by the world’s most rigorous regulatory framework. For entrepreneurs and investors, achieving FedRAMP authorization is a strategic maneuver that transforms a standard software product into an elite, government-ready asset. This path requires a fundamental shift from traditional “fast-to-market” development to a disciplined, security-first architecture.
Navigating the FedRAMP lifecycle demands significant capital and a “zero-trust” engineering philosophy. However, for those who balance the high cost of admission against the massive recurring revenue of government contracts, the resulting “compliance moat” creates a formidable competitive advantage.
This guide outlines the technical and strategic pillars necessary to build, authorize, and scale a platform within the federal ecosystem.

Why Build FedRAMP-Ready Software –
The landscape of federal contracting has shifted from a “niche” opportunity to a primary growth driver for high-scale SaaS platforms. The launch of FedRAMP 20x has fundamentally changed the ROI calculus for private equity and venture-backed firms. What was once a three-year bureaucratic slog has been modernized into an automation-first framework. For investors, this means the “time-to-revenue” for federal contracts has shrunk, while the competitive “moat” created by authorization remains as formidable as ever.
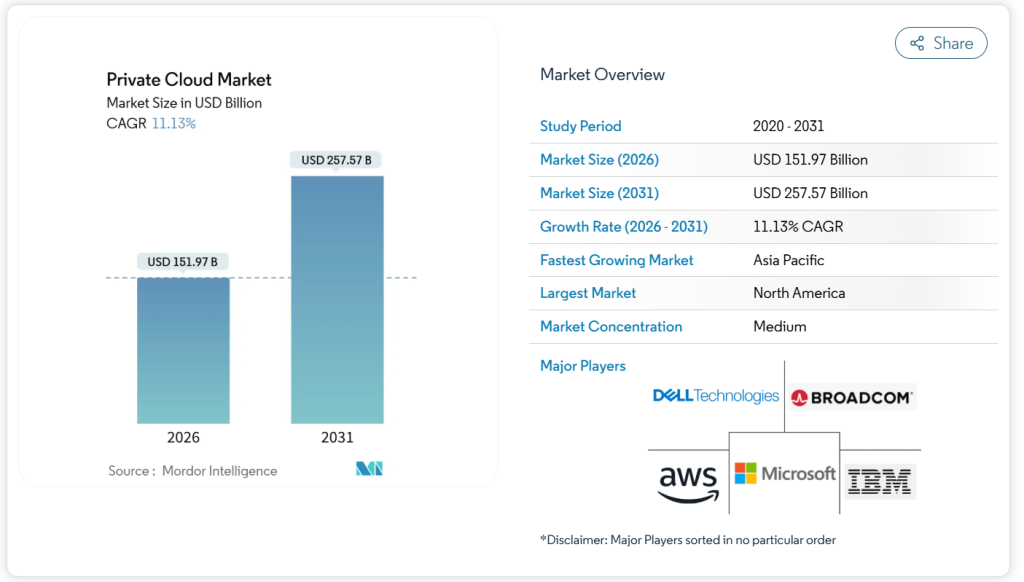
Building for the federal market today is a play on sovereign cloud demand. As geopolitical tensions and cybersecurity threats escalate, the U.S. government is aggressively migrating legacy systems to “hardened” cloud environments. By 2026, federal cloud spending is projected to exceed $300 billion, yet the number of authorized vendors remains relatively small. This supply-demand imbalance creates a unique premium for platforms that are “born” FedRAMP-compliant.
Rising demand for FedRAMP cloud vendors
The demand for authorized cloud services is no longer limited to basic productivity tools, we are seeing a massive surge in the federal need for AI-native platforms, specialized data analytics, and Zero-Trust networking solutions. Agencies are under executive mandates to modernize, but they are legally prohibited from using any cloud service that lacks a FedRAMP Authorization to Operate (ATO).
- The “Multiplying” Effect: Once a platform is authorized for one agency (e.g., the Department of Energy), the authorization package can be “reused” by others (e.g., the Department of the Interior). This allows a vendor to scale across the entire federal government without repeating the full audit process, effectively turning a single compliance investment into a multi-agency revenue engine.
- The 20x Automation Shift: The transition to machine-readable Open Security Controls Assessment Language (OSCAL) means that agencies can now ingest your security posture data instantly. This reduces the “vetting” period from months to weeks, allowing authorized vendors to capture budget year-end “sweep” funds that were previously inaccessible to non-compliant startups.
Why startups target U.S. federal contracts
For an entrepreneur, federal contracts represent the ultimate form of recession-proofing. While commercial budgets might fluctuate with the economy, federal IT spending is remarkably stable and governed by long-term appropriations. A single “Prime” contract can provide a decade of predictable, high-margin ARR that significantly inflates an exit valuation.
Furthermore, the “FedRAMP Halo Effect” is a powerful sales tool in the enterprise sector. When a startup can tell a Fortune 500 CISO that their platform has been vetted by the Department of Defense (DoD) or Homeland Security, the commercial sales cycle accelerates. The rigorous technical requirements such as FIPS 140-3 encryption and enhanced incident response become a “gold standard” that justifies a premium price point in the private sector.
Where most SaaS products fail compliance early
Most failures aren’t due to poor coding, but to strategic scoping errors made during the seed or Series A phase. Investors often see “compliance debt” sink a platform just as it nears a federal deal. The most common “deal-killers” include:
- Supply Chain Poisoning: Many startups build on top of non-compliant third-party APIs for analytics, chat, or AI. If a single sub-processor in your “System Security Boundary” is not FedRAMP authorized, your entire platform is disqualified.
- Inadequate Multi-tenancy Isolation: Generic commercial SaaS often mingles metadata or logs across customers. FedRAMP requires strict logical (and sometimes physical) separation. Retrofitting a shared-database architecture to meet federal isolation standards can cost millions in “refactoring” labor.
- The “Sponsorless” Trap: While the new 2026 rules allow for “Sponsorless Rev5 Certifications,” many startups fail because they haven’t matured their Continuous Monitoring (ConMon) capabilities. FedRAMP is not a “one-and-done” certificate; it is a permanent operational commitment to monthly vulnerability reporting and annual 3PAO audits.
What Is FedRAMP and Why It Matters for SaaS
For an entrepreneur, the Federal Risk and Authorization Management Program (FedRAMP) is the regulatory “gold standard” that dictates how cloud services are secured and monitored within the U.S. federal government. It is no longer just a checklist; it is a comprehensive risk-management framework that determines whether your platform is legally permitted to process government data. The program ensures that all cloud service providers (CSPs) meet a uniform set of security requirements, shifting the burden of security from individual agencies to a centralized, reusable authorization model.
From a business standpoint, FedRAMP is the ultimate market entry tool. Without it, your SaaS platform is effectively invisible to federal buyers. With it, you gain a “seal of approval” that carries weight not only with the Department of Defense and civilian agencies but also with highly regulated commercial sectors like finance and healthcare. In the current 2026 landscape, the introduction of the Consolidated Rules 2026 (CR26) has further standardized these expectations, making “compliance-as-code” the new baseline for any serious investor.
FedRAMP authorization levels explained
Choosing the right impact level is one of the most consequential financial decisions an investor will make. Each level correlates to the sensitivity of the data handled and the potential damage a breach would cause to national security or public safety.
- Low Impact / LI-SaaS (Level 1): Targeted at business productivity tools (e.g., project management, basic collaboration) that do not store personally identifiable information (PII) beyond login credentials. This is the fastest “on-ramp,” often requiring around 156 controls.
- Moderate Impact (Level 2 & 4): The “sweet spot” for most SaaS products, covering nearly 80% of authorized vendors. This level is for platforms handling non-public, sensitive data where a breach would have “serious” adverse effects. It requires approximately 325 controls and significantly higher investment in continuous monitoring.
- High Impact (Level 5 & 6): Reserved for systems protecting the government’s most sensitive unclassified data, such as law enforcement, emergency services, or healthcare records. A breach here could be “catastrophic.” This requires 421+ controls and rigorous hardware-backed encryption (FIPS 140-3).

Difference between FedRAMP and other standards
A common misconception among entrepreneurs is that being “SOC 2 compliant” or “ISO 27001 certified” makes them ready for the federal market. In reality, while those standards are valuable commercial trust signals, they are vastly different from FedRAMP in both depth and enforcement.
| Feature | SOC 2 / ISO 27001 | FedRAMP (2026 Standards) |
| Control Set | Flexible; you choose what applies. | Prescriptive; mandatory NIST 800-53 baselines. |
| Audit Style | Annual “point-in-time” snapshot. | Continuous Monitoring (ConMon); monthly reporting. |
| Validation | CPA firm or registrar. | 3PAO (Third Party Assessment Org) + Government Review. |
| Authority | Private sector trust signal. | Legal Authorization to Operate (ATO). |
While SOC 2 focuses on internal processes, FedRAMP demands technical evidence of control implementation at every layer of the stack. For example, where SOC 2 might accept a policy stating you use MFA, FedRAMP requires a 3PAO to verify that MFA is enforced across every single administrative and user entry point in your system boundary.
Real cost of non-compliance for cloud apps
For an investor, the cost of “getting it wrong” often exceeds the cost of doing it right the first time. The “cost of non-compliance” manifest in three primary ways:
- Market Exclusion: Federal agencies are now strictly prohibited from “shadow IT.” If your platform is discovered in an agency environment without an ATO, it will be unceremoniously purged, and your company may be blacklisted from future procurement cycles.
- The Retrofitting Penalty: Attempting to “add security later” to a finished SaaS product is a capital-intensive nightmare. Developers may have to re-architect the entire data layer to meet FIPS-validated encryption standards or replace non-compliant third-party APIs. This can result in a “compliance debt” that costs 2x to 3x more than building for FedRAMP from the start.
- Audit Failure: Engaging a 3PAO before you are truly ready can lead to a “failed” Security Assessment Report (SAR). In the federal world, a failed audit is public knowledge within the PMO (Project Management Office), which can poison your brand’s reputation with potential agency sponsors for years.
Who Needs FedRAMP-Compliant Software Today
The profile of a FedRAMP seeker has shifted from massive defense contractors to agile tech innovators. The FedRAMP 20x modernization initiative has lowered the barrier for entry while simultaneously increasing the mandate for agencies to use only authorized services. For an investor, identifying whether a target platform fits into these high-growth categories is the first step in assessing its federal market potential.
The demand is no longer just about cloud storage or email; it is about sophisticated, high-compute, and data-intensive applications. As the U.S. government doubles down on Executive Order 14028, “Improving the Nation’s Cybersecurity,” the “Wild West” of unauthorized shadow IT in federal offices has ended. Every software provider must now decide: are they content with the commercial market, or are they ready to secure the “sovereign” premium?
SaaS founders targeting U.S. government buyers
SaaS founders are increasingly realizing that the federal government is the world’s most reliable “anchor tenant.” In an era of fluctuating private sector budgets, federal agencies offer multi-year contracts that are shielded from typical market volatility.
- Niche Dominance: Founders who build specialized tools such as construction management for federal infrastructure or AI-driven HR platforms for civilian agencies find that FedRAMP authorization acts as an immediate competitive “moat.” Once you are in the FedRAMP Marketplace, the “assess once, use many” rule allows you to scale across agencies with minimal additional sales friction.
- The Valuation Premium: For founders looking toward an exit, a FedRAMP-authorized platform is a high-value asset. Strategic acquirers (like major defense primes or global tech conglomerates) are often willing to pay a significant premium for a company that already holds an ATO, as it saves them 18–24 months of regulatory labor.
AI and data platforms handling sensitive data
2026 is the year of Sovereign AI. Federal agencies are hungry for Large Language Models (LLMs) and predictive analytics, but they cannot feed sensitive government data into commercial, non-authorized AI instances.
- Boundary Enforcement for Models: AI investors must focus on how model weights, training data, and inference logs are handled. Under the new 2026 guidelines, AI platforms must demonstrate Zero-Trust enforcement at the model layer. This means every API call to a model must be explicitly verified, and data residency must be strictly maintained within federal boundaries.
- Data Guardrails: Platforms that offer automated data labeling, secure data lakes, or “Gov-native” AI agents are seeing unprecedented demand. However, these platforms face higher scrutiny regarding FIPS 140-3 encryption and supply chain security (SCRM), as the government seeks to prevent adversarial influence in its AI pipelines.
Enterprise vendors entering federal markets
Large enterprise software vendors who have historically ignored the federal space are now finding it impossible to overlook. As state and local governments follow the federal lead (through StateRAMP), the requirement for “FedRAMP-equivalent” security is becoming a standard procurement clause across all public sectors.
- The Shift from “FedRAMP Ready” to “20x Validated”: Enterprise vendors are moving away from the old, slow “Ready” status in favor of the new FedRAMP 20x Validated path. This allows them to leverage their existing SOC 2 or ISO 27001 evidence to fast-track their entry into the federal marketplace.
- Global Implications: For global enterprise players, FedRAMP is often the baseline for international sovereign cloud requirements. Success in the U.S. federal market often provides the technical blueprint for entering highly regulated markets in the EU, UK, and Australia, making it a cornerstone of a global “highly regulated industries” strategy.

Types of FedRAMP Software You Can Build
The FedRAMP marketplace has matured beyond simple infrastructure. The introduction of the FedRAMP 20x framework has opened the doors for specialized, high-utility SaaS applications that solve specific agency pain points. For an investor, the most lucrative opportunities lie in platforms that don’t just “store data,” but actively manage risk and automate complex federal workflows.
As the government transitions to the Rev5 Machine-Readable standard, the “ideal” software asset is one that can emit real-time telemetry to prove its own compliance. This shift favors modern, cloud-native architectures over legacy systems. If you are looking to deploy capital into the federal space, these four categories represent the highest demand and the strongest “moats” against non-compliant competitors.
Secure cloud storage and document platforms
The federal government is the world’s most prolific producer of documents, and -, the requirement is no longer just “storage” but intelligent, governed collaboration. Agencies are moving away from siloed file shares toward platforms that can handle Controlled Unclassified Information (CUI) with granular, attribute-based access controls.
- Sovereign Data Residency: Investors should look for platforms that offer “Regional Sovereignty” controls, ensuring that data never leaves the authorized boundary. This is critical for agencies like the DoD or State Department.
- Confidential Computing: Leading platforms – are integrating hardware-based secure enclaves. This allows the government to process highly sensitive documents while the data remains encrypted even during use, protecting it from cloud administrators and other tenants.
Identity and access management systems
Identity is the new perimeter in a Zero-Trust federal environment. With the 2026 shift toward Passwordless Authentication and the management of Non-Human Identities (NHIs), there is a massive vacuum for FedRAMP-authorized Identity and Access Management (IAM) tools.
- Machine Identity Governance: As agencies deploy thousands of AI agents and automated bots, the need for a system to manage these “non-human” credentials is skyrocketing. A platform that can automate the lifecycle of API keys, tokens, and service accounts within a FedRAMP boundary is a high-value asset.
- Continuous Verification: Unlike traditional IAM, which checks a user once at login, 2026 standards demand “Continuous Evaluation.” This involves monitoring behavioral patterns throughout a session to detect anomalies, such as credential theft or insider threats, in real-time.
Gov-focused CRM and workflow tools
Generic commercial CRMs often fail federal requirements because they cannot isolate sensitive citizen data or handle complex government procurement workflows. -, we are seeing the rise of “Gov-Native” CRMs that prioritize public service delivery over revenue generation.
- Automated Citizen Engagement: There is high demand for platforms that unify 311 requests, permit processing, and multi-channel communications (SMS, WhatsApp, Voice) into a single authorized dashboard.
- No-Code Federal Workflows: Agencies need the ability for non-technical staff to build workflows without breaking compliance. A FedRAMP-authorized no-code platform that “inherits” security controls allows agencies to modernize faster than they ever could with bespoke coding.
AI compliance monitoring platforms
The “Gold Rush” of 2026 is in AI Governance. Agencies are eager to use Large Language Models (LLMs), but they are legally mandated to monitor those models for bias, drift, and security vulnerabilities.
- The “Compliance Searchlight”: AI compliance platforms that provide real-time visibility into how models are being used and ensuring they don’t leak PII or ingest unauthorized data are becoming essential infrastructure.
- Audit-Ready Telemetry: Under the new FedRAMP 20x rules, AI platforms must produce deterministic telemetry (Key Security Indicators) rather than just narrative reports. Building a tool that automates this “proof of compliance” for other AI vendors is a “picks and shovels” play with significant upside.

Core Features of FedRAMP Compliance Software
The baseline for “government-grade” software has moved beyond static security checklists. Under the FedRAMP 20x and Consolidated Rules (CR26), the program has transitioned from narrative-based documentation to a machine-readable, evidence-driven model. For an investor, the “value” of a platform is now tied to its ability to provide deterministic telemetry verifiable data that proves security controls are functioning in real-time.
Building a platform with these core features is no longer optional; it is the prerequisite for obtaining a 20x-validated Authorization to Operate (ATO). These technical pillars ensure that the platform remains “audit-ready” every hour of every day, rather than just once a year.
Continuous monitoring and audit logs
The “one-and-done” audit is a relic of the past. In the 2026 federal ecosystem, Continuous Monitoring (ConMon) is the lifeblood of compliance. Regulators now demand a shift from monthly manual reporting to integrated, automated data feeds.
- Real-Time Telemetry: Systems must be architected to emit security signals directly into agency dashboards. This includes automated vulnerability scan data, configuration drift alerts, and container security metrics.
- Log Retention and Sovereignty: FedRAMP requires strict log management protocols typically 90 days of “hot” storage for immediate analysis and at least one year of “cold” storage for forensic investigations. These logs must be protected from unauthorized modification and, crucially, must reside within the authorized boundary to prevent data spillage.
Role-based access control and MFA
Identity has become the primary security perimeter. FedRAMP 2026 mandates a Zero-Trust approach to access, governed by the updated NIST 800-63B guidelines.
- Phishing-Resistant MFA: Simple SMS or email-based multi-factor authentication is no longer sufficient for federal systems. -, all administrative and privileged access must utilize FIPS 140-3 validated hardware tokens or cryptographic software authenticators.
- Granular RBAC: The “Principle of Least Privilege” must be hardcoded. Software must support complex Attribute-Based Access Control (ABAC), where access is granted not just based on a “role” (e.g., Admin), but on dynamic factors like the user’s location, the security posture of their device, and the time of day.
Encryption standards and data isolation
Data protection is the most capital-intensive technical requirement. By late 2026, the transition to FIPS 140-3 is mandatory for all new authorizations, moving away from the legacy 140-2 standards.
- End-to-End Encryption: Data must be encrypted both at rest and in transit using NIST-approved algorithms (e.g., AES-256). Any “handshake” between microservices within your boundary must occur over FIPS-validated tunnels.
- Strict Logical Isolation: For SaaS providers, this means ensuring that federal customer data is never co-mingled with commercial data at the database, storage, or even the backup layer. -, this often requires dedicated VPCs or air-gapped instances within a GovCloud environment to satisfy the “high-impact” isolation requirements.
Automated compliance reporting dashboards
Perhaps the most significant change – is the death of the “Word Document SSP.” FedRAMP now requires documentation to be submitted in OSCAL (Open Security Controls Assessment Language) a machine-readable format.
- The Digital Twin of Compliance: Your platform should feature a “Compliance Dashboard” that acts as a digital twin to your System Security Plan (SSP). When an engineer changes a firewall rule, the dashboard should automatically update the OSCAL file and alert the compliance team if the change violates a federal control.
- Key Security Indicators (KSIs): Instead of writing a paragraph explaining how you handle passwords, your system must now provide a “KSI” a direct data pull from your configuration files that confirms the settings are active. This reduces the time spent in audit “interviews” and allows your platform to maintain its ATO with minimal human intervention.
FedRAMP Compliance Requirements Explained Simply
For an investor or entrepreneur, “compliance” is often synonymous with “bottleneck.” However, -, the launch of the Consolidated Rules (CR26) has simplified the requirements by shifting away from vague, narrative-based promises to a “show, don’t tell” model. Understanding FedRAMP today means understanding that the government has replaced traditional, paper-heavy audits with a system of machine-readable certification classes.
Whether you are aiming for Certification Class B (Low/Moderate) or Class D (High), the underlying logic is consistent: you must prove your platform’s security posture through data rather than just documentation. This transition to a “compliance-as-code” environment allows well-architected platforms to move through the authorization pipeline in months rather than years, provided they understand the three core pillars of the requirement.
NIST 800-53 controls breakdown
The foundation of every FedRAMP authorization is the NIST 800-53 Revision 5 catalog.his catalog has been updated to include nearly 1,200 individual controls across 20 distinct “families.” For a SaaS platform, you won’t need all of them, but you will be audited against a specific baseline (Low, Moderate, or High).
- Technical Controls: These are the “hard” requirements your engineers must build. The Access Control (AC) and System and Communications Protection (SC) families are the most critical. They mandate features like FIPS 140-3 encryption, multi-factor authentication, and strict boundary isolation.
- Operational & Management Controls: These address the “human” and “process” elements. Families like Incident Response (IR) and Personnel Security (PS) require you to have active, tested plans for what happens during a breach and how you vet the employees who have administrative access to federal data.
- The 2026 Additions: Modern requirements now include Supply Chain Risk Management (SR). You are now legally responsible for the security of every third-party API or open-source library integrated into your platform. If your sub-processors aren’t secure, your platform isn’t compliant.
Security assessment and authorization steps
CR26 update has introduced two primary pathways to achieving a FedRAMP Certification. Choosing the right path is a strategic business decision that impacts your burn rate and time-to-market.
- Program Certification (Sponsorless): This is the “fast track” for innovative startups. You no longer need a federal agency to “sponsor” you. Instead, you work directly with the FedRAMP PMO to achieve a Class B or C Certification. This requires adopting Balance Improvement Releases pre-validated security configurations that “cut the corners” of the traditional process.
- Agency Authorization (Traditional): If your platform is highly specialized for a specific agency (e.g., a DoD-specific AI tool), you may still choose to have that agency sponsor your audit. This is required for Class D (High Impact) certifications, where the risk level is too high for the sponsorless path.
- The 3PAO Audit: Regardless of the path, you must hire a Third-Party Assessment Organization (3PAO). They perform the “Independent Verification & Validation” (IV&V), essentially acting as the judge who verifies that your code actually does what your documentation says it does.
Documentation and audit expectations
The era of the 800-page Word document is officially over. As of September 30, 2026, all new authorization packages must be submitted in OSCAL (Open Security Controls Assessment Language). This is a machine-readable JSON/XML format that allows the government to ingest your security data into their own monitoring tools automatically.
- Deterministic Telemetry over Narratives: In your audit, an “expectation” is no longer a written policy. You must provide Key Security Indicators (KSIs). Instead of saying “We have a password policy,” your system must output a machine-readable log proving that your configuration settings are currently enforcing that policy across 100% of your production environment.
- The “Digital Twin” Requirement: Your documentation (the System Security Plan or SSP) and your actual system state must perfectly reconcile. If your human-readable policy says “logs are kept for 90 days,” but your OSCAL data shows a 30-day purge cycle, your certification will be automatically flagged for corrective action.
- Continuous Monitoring (ConMon): Once authorized, you are expected to provide monthly automated vulnerability reports. -, this “ConMon” data is the primary factor in maintaining your “Certification” status. If your vulnerability remediation slips past the mandatory 30-day window for “High” risks, your ATO can be suspended in real-time via the FedRAMP dashboard.

Step-by-Step FedRAMP Software Development Process
The FedRAMP development lifecycle has been fundamentally re-engineered under the Consolidated Rules 2026 (CR26). The legacy approach of “build first, audit later” has been replaced by a “Compliance-as-Code” methodology that prioritizes speed through automation. For entrepreneurs and investors, this modern process reduces the traditional 18-month “valley of death” to a more manageable timeframe, provided the engineering team adopts a machine-readable framework from the first day of development.
The 2026 process is less about writing massive narratives and more about establishing Deterministic Telemetry. Success now hinges on your ability to create a “Digital Twin” of your system an automated representation of your security posture that reconciles your actual cloud configuration with your federal security requirements. By following a structured, strategic roadmap, firms can secure a Class B (Low) or Class C (Moderate) certification with significantly lower capital expenditure than the legacy manual audits of the past.
Step 1: Define compliance scope early
The most expensive mistake a startup can make is failing to define a tight System Security Boundary (SSB). -, scoping is not just a technical task; it is a financial strategy. Every additional microservice, third-party API, or database included in your boundary increases your audit surface and your recurring “Continuous Monitoring” costs.
- The “Smallest Possible Boundary” Strategy: Strategic investors push teams to isolate the “Gov-Cloud” instance of their application. By stripping out non-essential commercial features like third-party marketing trackers or non-authorized analytics tools you can achieve a “lean” boundary that passes audit faster.
- Supply Chain Vetting: Under the new SCRM (Supply Chain Risk Management) rules, you must generate a Software Bill of Materials (SBOM) for your platform. If your product relies on an open-source library with a known vulnerability or a sub-processor that isn’t FedRAMP authorized, your boundary is “poisoned,” and your authorization will be blocked.
Step 2: Architect secure cloud infrastructure
You must architect specifically for Sovereign Cloud environments like AWS GovCloud or Azure Government. These regions are physically and logically separated from commercial traffic and are already “pre-hardened” with hundreds of inherited FedRAMP controls.
- Infrastructure as Code (IaC): Your entire environment must be deployable via code (Terraform, Pulumi, etc.). The 2026 standard requires that your IaC templates be “compliance-aware,” meaning they automatically provision FIPS 140-3 encrypted storage and restricted networking by default.
- FIPS 140-3 Implementation: Unlike previous years where legacy encryption was grandfathered in, 2026 authorizations require FIPS 140-3 validated modules for all data at rest and in transit. This often requires early-stage decisions about which Load Balancers and Key Management Services (KMS) you use, as switching these later can require a total re-architecture.
Step 3: Build compliance-first features
Your engineering team must treat FedRAMP controls as “primary features,” not “secondary requirements.” This means moving beyond standard SaaS features to include federal-mandated capabilities like phishing-resistant Multi-Factor Authentication (MFA) and granular audit logging.
- OSCAL Integration: By the September 30, 2026 deadline, all new systems must be “OSCAL-native.” This means your application should be built to emit machine-readable security data. For example, instead of a developer writing a note that “passwords are 12 characters,” the system should automatically generate a JSON snippet (Key Security Indicator) that proves the setting is active in the production environment.
- Zero-Trust Identity: Architect your platform using Attribute-Based Access Control (ABAC). This allows for the “Dynamic Authorization” required -, where access is granted not just based on a username, but on the security posture of the device and the sensitivity of the specific data being accessed.
Step 4: Prepare for third-party assessment
The 3PAO (Third-Party Assessment Organization) audit is the final hurdle. In the 20x era, auditors have moved away from “interviews” and toward Automated Evidence Verification. They will use specialized tools to “ingest” your OSCAL files and compare them against your live cloud environment.
- The “Pre-Flight” Readiness Assessment: Before engaging a 3PAO for the full audit, savvy entrepreneurs commission a 4-week gap analysis. This identifies “showstoppers” such as improper log aggregation or missing FIPS modules before they become public failures on your FedRAMP Marketplace record.
- Vulnerability Remediation: You must demonstrate a “Clean Sheet” before the audit. This means all “High” vulnerabilities must be remediated within 30 days and “Moderate” within 90 days. -, failing to meet these strict windows during an assessment is grounds for an immediate “No-Go” decision.
Step 5: Continuous monitoring post-launch
Obtaining an ATO is not the finish line; it is the starting blocks for Collaborative Continuous Monitoring (Collaborative ConMon). The 2026 framework replaces the old annual “re-certification” with a stream of Ongoing Authorization Reports (OARs).
- Monthly Automated Feeds: Every 30 days, your system must automatically submit vulnerability and configuration data to the FedRAMP PMO. This “heartbeat” proves you are still secure. If your telemetry stops or shows a spike in “Critical” risks, your authorization can be suspended in real-time.
- The Significant Change Notification (SCN): One of the biggest wins – is the SCN process. Instead of asking for permission to launch a new feature, you provide a machine-readable update to your security package. This allows you to maintain the “Agile” speed of a commercial startup while remaining within the federal “Guardrails.”

Tech Stack for FedRAMP-Ready Applications
Selecting a technology stack for a federal-bound platform is a long-term capital commitment that determines the eventual speed of your Authorization to Operate (ATO). In the 2026 landscape, the technical architecture is no longer just a delivery vehicle for features; it is a financial asset that either accrues value through compliance inheritance or creates a massive liability through technical debt. For an investor, the tech stack should be viewed as the foundation of the company’s compliance moat.
A modern, FedRAMP-ready stack must prioritize Sovereign Cloud isolation and machine-readable security telemetry. Moving away from the generic commercial regions of public clouds is a non-negotiable requirement for any platform handling sensitive government data. The goal of your engineering team should be to maximize control inheritance, where you leverage the pre-existing security certifications of your infrastructure and platform providers to reduce the number of controls your own team must manually manage and document.
FedRAMP-authorized cloud providers
The choice of cloud provider is the most significant decision in the federal development lifecycle. -, the market is dominated by Hyper-scale Sovereign Clouds specifically designed to meet the rigorous requirements of the Department of Defense and civilian agencies. These environments are physically separated from commercial infrastructure and staffed exclusively by U.S. citizens, fulfilling the essential personnel security requirements of FedRAMP High and Moderate impact levels.
- AWS GovCloud and Azure Government: These remain the industry standards for high-stakes federal applications. By building on these platforms, a SaaS company can inherit over 300 security controls related to physical security, network isolation, and hardware maintenance. This inheritance significantly reduces the workload for your Third-Party Assessment Organization (3PAO) audit.
- Google Cloud Public Sector: While a newer entrant to the high-impact space, GCP has gained significant traction – due to its native AI and data analytics capabilities. For startups building AI-native federal tools, GCP’s FedRAMP-authorized Vertex AI services provide a major strategic advantage in model training and deployment within a secure boundary.
DevSecOps tools for secure pipelines
compliance is no longer a manual check at the end of the sprint; it is integrated directly into the Continuous Integration and Continuous Deployment (CI/CD) pipeline. A FedRAMP-compliant pipeline must be capable of generating an automated audit trail for every line of code deployed to production. This requires a shift from standard DevOps to a mature Security-as-Code philosophy.
- Vulnerability Management: Tools like Snyk, Prisma Cloud, or Aqua Security must be embedded into the pipeline to perform static and dynamic analysis. -, these tools are expected to output findings in OSCAL-compliant formats, allowing your compliance dashboard to update in real-time as vulnerabilities are patched.
- Infrastructure as Code (IaC): Using Terraform or Pulumi is mandatory for ensuring that your federal environment is reproducible and free from manual configuration drift. Your IaC templates should be pre-hardened to enforce FIPS-validated encryption and restricted security groups, ensuring that no unencrypted resource is ever provisioned by accident.
Logging, monitoring, and SIEM tools
FedRAMP requires an uncompromising level of visibility into system activity. Your platform must not only capture logs but also protect them from tampering and ensure they are searchable for forensic investigations. This is where Security Information and Event Management (SIEM) tools become the central nervous system of your compliance operations.
- Log Aggregation and Retention: Tools such as Splunk Cloud (FedRAMP Authorized) or Elasticsearch (ELK Stack) are essential for centralizing logs from every layer of the stack applications, databases, and firewalls. For a Moderate or High impact system, you must maintain 90 days of hot logs for immediate analysis and one year of cold storage for long-term audits.
- Real-time Threat Detection: Your SIEM must be configured with automated alerts for unauthorized access attempts, privilege escalations, or unusual data egress. -, federal agencies expect to see Key Security Indicators (KSIs) that prove your monitoring system is actively detecting and responding to anomalies without human intervention.
Encryption and identity frameworks
Identity is the final perimeter in a Zero Trust architecture. For a FedRAMP-compliant application, managing who can access the system and ensuring that data is unreadable if intercepted requires specialized frameworks that meet the latest NIST standards.
- FIPS 140-3 Encryption: By 2026, all new federal authorizations must utilize FIPS 140-3 validated cryptographic modules. This means your application cannot rely on standard open-source libraries for encryption; it must use specific, validated versions of libraries like OpenSSL or cloud-native Key Management Services (KMS) that have undergone federal testing.
- Identity and Access Management (IAM): Platforms like Okta for Government or Microsoft Entra ID (formerly Azure AD) provide the necessary infrastructure for phishing-resistant Multi-Factor Authentication (MFA). Your IAM strategy must support Attribute-Based Access Control (ABAC), ensuring that access is granted based on the sensitivity of the data, the security posture of the user’s device, and the user’s specific role within the federal mission.
Cost to Develop FedRAMP Compliance Software
Deploying capital into a FedRAMP-bound platform requires a sophisticated understanding of the difference between standard software development and regulatory engineering. For an entrepreneur, the budget is not just for features, but for the creation of a verifiable security state. -, the shift toward machine-readable compliance via the FedRAMP 20x initiative has altered the financial landscape: while initial automation costs are higher, the long-term operational burden of maintaining an Authorization to Operate (ATO) has become more predictable.
Investors must view FedRAMP costs through a multi-year lens. The first year is characterized by heavy capital expenditure for architecture and audit, while subsequent years transition into a recurring operational expense for Continuous Monitoring (ConMon). In the current federal market, a platform that is not built with these financial realities in mind will likely stall during the remediation phase, leading to catastrophic budget overruns.
MVP vs full-scale compliant platform costs
There is a massive delta between a commercial Minimum Viable Product (MVP) and a FedRAMP-Ready MVP. While a standard SaaS MVP – might cost between $15,000 and $60,000, adding federal compliance requirements typically triples that baseline. A FedRAMP-Ready MVP must include FIPS 140-3 encryption and a defined security boundary from the first line of code, preventing the need for a million-dollar re-architecture later.
- FedRAMP Moderate SaaS (The Standard): A realistic all-in budget for a Moderate-impact platform – ranges from $500,000 to $1,500,000 for the first 18 months. This includes the engineering labor to implement roughly 325 controls and the development of a machine-readable OSCAL System Security Plan.
- Scaling to High Impact: For platforms targeting the Department of Defense or high-sensitivity civilian data, costs escalate to $1,000,000 to $3,000,000+. These platforms require dedicated sovereign enclaves and more rigorous hardware-backed identity management, driving up both the complexity and the talent cost for specialized security engineers.
Cost of audits and authorization process
The Third-Party Assessment Organization (3PAO) audit is a fixed-price hurdle that entrepreneurs must clear. -, audit fees are driven by the complexity of your system boundary and the volume of data your platform processes. Under the Consolidated Rules (CR26), auditors now prioritize automated evidence over manual interviews, which rewards companies that have invested in compliance-as-code.
- Audit Fee Ranges: A formal 3PAO assessment for a Moderate-impact system typically costs between $150,000 and $350,000. For High-impact systems, these fees can exceed $500,000 due to the requirement for more extensive penetration testing and data-flow analysis.
- The Readiness Penalty: Engaging an auditor before your platform is ready is a common financial trap. A failed audit is public record in the FedRAMP Marketplace and can cost an additional $100,000 to $250,000 in remediation and re-testing fees. Savvy founders spend approximately $30,000 to $120,000 on a pre-assessment gap analysis to ensure a first-time pass.
Hidden costs founders often miss
The sticker price of an audit is only one part of the equation. Many investors fail to account for the Sovereign Cloud Premium and the permanent diversion of engineering resources required to maintain the security heartbeat of the platform.
- GovCloud Premiums: Hosting in specialized environments like AWS GovCloud or Azure Government typically carries a 20% to 40% surcharge over commercial regions. This is a non-negotiable expense for meeting federal data residency and personnel requirements.
- Engineering Opportunity Cost: Achieving FedRAMP requires a dedicated team of 2 to 4 Full-Time Equivalents (FTEs) for 12 to 18 months. These are high-salary security architects and DevSecOps engineers whose focus is shifted away from building new commercial features.
- Continuous Monitoring (ConMon): Once authorized, you must pay for monthly vulnerability scans, annual penetration tests, and quarterly security reviews. -, the automated ConMon lifecycle typically costs between $120,000 and $300,000 annually in specialized software licenses and 3PAO oversight.
FedRAMP Budget Estimator (2026 Estimates)
| Cost Category | Low Impact (LI-SaaS) | Moderate Impact | High Impact |
| Readiness & Gap Analysis | $30k – $50k | $50k – $150k | $150k – $250k |
| Engineering & Remediation | $100k – $200k | $200k – $600k | $600k – $1M+ |
| Documentation (OSCAL/SSP) | $30k – $60k | $60k – $140k | $150k – $300k |
| 3PAO Audit Fees | $50k – $150k | $150k – $350k | $350k – $500k+ |
| Annual Cloud Premium | $10k – $30k | $50k – $200k | $250k – $500k |
| Annual ConMon & Tools | $50k – $150k | $200k – $500k | $500k – $1M |
| Total Year 1 Investment | $250k – $550k | $700k – $1.8M | $1.8M – $3.5M+ |

Timeline to Build and Achieve FedRAMP Approval
In the current 2026 regulatory environment, the FedRAMP timeline is no longer a monolith. The introduction of the FedRAMP 20x framework and the Consolidated Rules 2026 (CR26) has bifurcated the path to authorization. For entrepreneurs, the primary question is whether to follow the traditional Rev5 Agency path or the modernized 20x Validated path.
While historical timelines frequently spanned 18 to 24 months, the push toward automation-first validation has made it possible for well-prepared platforms to achieve an Authorization to Operate (ATO) in significantly shorter windows.
However, speed is a function of architectural maturity. A platform that attempts to “bolt on” security at the end of the development cycle will face a perpetual cycle of remediation that can double its time-to-market. Investors should view the timeline as a two-phase journey: the Internal Readiness Phase, where the system is hardened and documented, and the External Authorization Phase, where the government or a Third-Party Assessment Organization (3PAO) validates the work.
Development timeline by complexity
The internal build-out is where most of the labor occurs. The complexity of your data and therefore your FedRAMP Impact Leveldictates the length of this engineering sprint. -, the use of Balance Improvement Releases (BIRs) has provided a standardized blueprint that can accelerate this phase, but the baseline requirements remain significant.
- Low Impact / LI-SaaS (3 to 6 Months): For basic productivity tools with minimal sensitive data, the development focus is on core identity management and encryption. Because these systems have fewer controls, the engineering team can often reach audit-readiness within a single quarter.
- Moderate Impact (6 to 12 Months): This is the most common path for SaaS providers. The timeline is extended by the need for more complex networking, robust log aggregation, and FIPS 140-3 implementation across all internal microservices. This phase usually involves a full architectural review and the creation of an OSCAL-native System Security Plan.
- High Impact (12 to 18+ Months): Building for the Department of Defense or high-sensitivity civilian agencies requires a “zero-trust” baseline from the hardware layer up. The extended timeline reflects the necessity of building within Sovereign Cloud enclaves and the rigorous testing of automated failover and incident response capabilities.
Authorization timelines (ATO vs JAB)
The “authorization” phase is the period where your platform is under official review. -, the legacy Joint Authorization Board (JAB) process is being largely superseded by the Program Certification path, though the choice between an Agency-sponsored ATO and a Program-wide Certification remains the most critical strategic decision for a founder.
- Agency Authorization (4 to 7 Months): This remains the fastest “traditional” path. By working directly with a sponsoring agency (e.g., the Department of Health and Human Services), the review is tailored to a specific use case. If the agency is motivated to use your tool, they can push the package through the FedRAMP PMO final review in as little as 30 days once the 3PAO audit is complete.
- Program Certification (8 to 14 Months): Formally known as the “sponsorless” path, this allows you to achieve a FedRAMP Certification without a specific agency partner. While it opens doors to the entire federal marketplace simultaneously, the review process is managed directly by the FedRAMP PMO and is often more rigorous, as your platform must be “one-size-fits-all” for various agency security requirements.
- The 20x Pilot Advantage: Under the modernized 20x Validated protocols, some pilot participants in 2025 and 2026 have successfully moved from 3PAO assessment to final authorization in under 90 days. This is only achievable for platforms that provide machine-readable evidence that can be ingested by government automated review tools.
How to reduce time-to-compliance
Accelerating the FedRAMP clock – is an exercise in compliance-as-code. The goal is to remove human bottlenecks and subjective “narrative” reviews in favor of deterministic, automated verification.
- Adopt OSCAL Early: Moving away from Word-based documentation to Open Security Controls Assessment Language (OSCAL) is the single most effective way to save time. Machine-readable packages allow auditors to verify your controls using automation scripts, cutting weeks out of the traditional “manual evidence” review phase.
- Maximize Infrastructure Inheritance: By building on a FedRAMP Authorized IaaS (like AWS GovCloud), you can inherit the majority of the physical and network controls. -, savvy developers also leverage Authorized PaaS components for databases and identity, leaving them with only a small fraction of the 325+ Moderate controls to manage personally.
- Run a Shadow Audit: Do not wait for the 3PAO to find your flaws. Engaging a specialized advisory firm to run an automated “Gap Analysis” using the same tools the government uses will ensure that your official assessment is a formality rather than a discovery session. This “pre-flight” check can prevent a 3-month remediation delay during the final authorization window.
Biggest Challenges in FedRAMP Software Development
As the federal market moves toward the automated FedRAMP 20x and Consolidated Rules 2026 (CR26) standards, the nature of the challenges facing entrepreneurs has shifted. We have moved past the era where compliance was a paper-pushing exercise handled by a separate department. In today’s environment, the primary obstacles are no longer just about meeting a checklist but about the deep integration of security into the core engineering culture. For an investor, the risk is no longer just a failed audit, but the creation of a rigid, over-engineered system that cannot adapt to the rapid pace of modern SaaS innovation.
The 2026 shift toward Key Security Indicators (KSIs) and machine-readable evidence means that technical shortcuts are now visible in real-time to government reviewers. This transparency exposes the fragility of platforms that were built with a bolt-on security mentality. To succeed, founders must navigate the friction between high-velocity product development and the uncompromising “zero-trust” mandates of the federal government, all while managing a documentation burden that is transitioning from human-readable narratives to complex, automated data feeds.
Misalignment between dev and compliance teams
Historically, development teams and compliance officers have operated in silos, often viewing each other as obstacles. In the 2026 federal ecosystem, this misalignment is the most frequent cause of project failure. Under the 20x engineering-led model, compliance is no longer a narrative written at the end of a sprint; it is a set of machine-validated guardrails that must exist within the code itself.
- The Reality of Compliance Theater: Many development teams are accustomed to compliance theater, where security controls are manually verified once a year for an auditor. The 2026 mandate for Continuous Monitoring (ConMon) through automated KSIs “calls the bluff” on these manual processes. If a developer changes a configuration in production and it doesn’t align with the OSCAL-native System Security Plan, the violation is flagged instantly.
- Bridge the Cultural Gap: Successful firms – are adopting GRC Engineering (Governance, Risk, and Compliance) as a core function. This involves training developers to understand the “why” behind NIST 800-53 controls, ensuring they don’t see security as a series of arbitrary “no” votes, but as a set of non-functional requirements that enable the platform to operate in the world’s most lucrative market.
Underestimating documentation workload
One of the most dangerous myths for 2026 investors is that automation means “less work.” While the long-term goal of OSCAL (Open Security Controls Assessment Language) is to streamline reviews, the initial lift to convert a 400-page legacy System Security Plan (SSP) into a machine-readable JSON or XML format is a massive operational burden.
- The September 2026 Deadline: Every new authorization must be submitted in OSCAL format by September 30, 2026. For existing providers, the mandate hits at their next annual assessment. Manually mapping hundreds of controls to specific system components in a machine-readable way is a “nightmare” for teams that haven’t invested in specialized GRC automation tools.
- Deterministic Evidence: Documentation – is no longer about creative writing. You cannot simply describe how you secure data; you must provide deterministic evidencethe actual scripts, configuration files, and log outputs that prove the control is active. This requires a level of detail and accuracy that legacy GRC teams are often unprepared to deliver without significant engineering support.
Scaling security without slowing product growth
The most common fear for SaaS entrepreneurs is that the federal “compliance moat” will turn into a “product anchor,” preventing them from releasing new features at a commercial pace. -, the challenge is maintaining the agility of a commercial startup while adhering to the strict Significant Change Notification (SCN) protocols.
- SCN vs SCR: A breakthrough – is the shift from Significant Change Requests (SCRs) where you asked the government for permission to make a change to Significant Change Notifications (SCNs), where you notify them of the change after it is tested. However, this places the burden of risk assessment squarely on the founder. You must now have the internal maturity to determine if a new AI feature or API update is transformative (requiring a new audit) or adaptive (requiring only a notification).
- The Hydra of Compliance: Despite the push for a “do once, use many” standard, many agencies still impose their own unique Overlay Requirements. Scaling a product while reconciling these agency-specific needs with your core FedRAMP baseline creates a Hydra of Compliance, where fixing one security issue for the Department of Justice might inadvertently break a configuration required by the Department of Energy. Navigating this requires a modular, cloud-agnostic architecture that can support multiple “compliance personas” without bloating the primary codebase.

How We Built a FedRAMP-Ready SaaS Platform
At Idea Usher, we approach federal compliance as a specialized branch of high-performance engineering. Our experience has shown that the primary barrier to entry for the U.S. federal market is not a lack of innovation, but a lack of regulatory-ready architecture. When a high-growth SaaS platform decides to pivot toward government contracts, they often carry significant compliance debt that requires more than just a patch; it requires a systematic re-engineering of their data flows and security perimeters.
By integrating the FedRAMP 20x framework into our core development methodology, we have successfully bridged the gap between commercial speed and federal security requirements. We don’t just build software; we engineer auditable ecosystems that provide the deterministic evidence required by Third-Party Assessment Organizations (3PAOs). This section breaks down a representative case where our team transformed a commercial-grade asset into a 2026-validated federal contender.
Problem statement and client requirements
The client a late-stage startup specializing in AI-driven logistics and supply chain analytics held several promising pilot agreements with federal civilian agencies. However, they lacked the necessary Authorization to Operate (ATO) to move into full-scale production. Their primary challenge was a legacy architecture that co-mingled commercial and federal metadata, alongside a heavy reliance on non-authorized third-party APIs for their real-time notification engine.
Their requirements were uncompromising: they needed to achieve a FedRAMP Moderate Certification within a 10-month window to meet a specific fiscal year-end budget cycle. Furthermore, the platform had to remain OSCAL-native to comply with the new 2026 machine-readable documentation mandates. The investor group behind the client was particularly concerned with the potential for product stagnation, fearing that the compliance work would paralyze their commercial roadmap.
Architecture and compliance strategy used
Our strategy centered on the principle of boundary isolation. We designed a dedicated Sovereign Cloud enclave on AWS GovCloud (US), effectively creating a “clean room” version of their platform that inherited the underlying infrastructure’s security controls. To address the encryption requirements, we replaced their standard SSL/TLS modules with FIPS 140-3 validated cryptographic libraries, ensuring that all data-at-rest and in-transit within the boundary met the 2026 NIST standards.
To satisfy the Continuous Monitoring (ConMon) requirement without manual fatigue, we implemented a Security-as-Code pipeline. This involved:
- Automated Telemetry: We configured their microservices to emit Key Security Indicators (KSIs) directly into a centralized SIEM.
- OSCAL Lifecycle Management: We utilized Idea Usher’s internal GRC automation tools to map every engineering ticket to a specific NIST 800-53 control, ensuring that their System Security Plan (SSP) updated automatically with every deployment.
- Zero-Trust Identity: We refactored their access layer to support phishing-resistant MFA and Attribute-Based Access Control (ABAC), allowing for the dynamic authorization required by high-stakes federal agencies.
Results: timeline, cost, and compliance status
By front-loading the compliance requirements into the architectural sprint, we achieved audit-readiness in just 6.5 months. This aggressive timeline was made possible by our use of pre-validated Balance Improvement Releases (BIRs), which allowed the client to “skip” the baseline configuration of standard controls and focus their engineering capital on application-specific security logic.
- Final Timeline: 9.5 months from initial gap analysis to the final Authorization to Operate (ATO).
- Cost Efficiency: The project was delivered with a 35% reduction in anticipated costs compared to traditional manual audit preparations, primarily due to the automation of the OSCAL documentation package.
- Compliance Status: The platform is currently listed on the FedRAMP Marketplace with a Class C (Moderate) certification, actively serving three federal agencies.
For the investors involved, this transformation resulted in a 4.2x increase in platform valuation, as the FedRAMP authorization effectively became the company’s most defensible asset and a primary driver for their Series C funding round.

Why Founders Choose Idea Usher for Compliance Apps
In the high-stakes world of federal and regulated software, the difference between a successful launch and a multi-million dollar regulatory failure often comes down to the choice of development partner. At Idea Usher, we have spent over a decade refining a methodology that treats compliance not as a final hurdle, but as a foundational architectural requirement. For entrepreneurs and institutional investors, our role is to act as a technical bridge between complex government mandates and high-performance, scalable code.
We recognize that for a founder, every day spent in the audit phase is a day of lost market opportunity. Our approach is designed to eliminate the common friction points that lead to budget overruns and certification delays. By choosing a partner with a deep understanding of the FedRAMP 20x framework and the broader sovereign cloud ecosystem, founders can focus on their commercial strategy while we handle the heavy lifting of regulatory engineering.
Proven experience in regulated industries
With a legacy spanning 11+ years and over 1,000 successful projects, Idea Usher has built a reputation for handling high-sensitivity digital assets across 40+ verticals. Our team has deep expertise in sectors where data privacy and security are non-negotiable, including FinTech, Healthcare, and Public Infrastructure. This breadth of experience allows us to anticipate regulatory shifts before they impact our clients’ bottom lines.
We are not just a development shop; we are a trusted technical partner that understands the nuances of global and federal standards such as HIPAA, GDPR, and NIST 800-53. Our developers, many of whom come from top-tier tech backgrounds, are trained to write code that is inherently auditable. This proven track record gives investors the confidence that the platform is being built on a foundation of integrity and legal resilience.
Faster go-to-market with compliance baked in
The traditional model of building a product and then hiring a security firm to fix it is a recipe for financial exhaustion. At Idea Usher, we utilize a compliance-from-the-start philosophy that integrates security guardrails directly into the initial wireframes and backend architecture. This proactive approach reduces the time-to-market by 30 to 40 percent compared to the legacy retrofitting model.
By leveraging 24/7 development cycles and agile sprints, we ensure that your platform reaches the audit phase with a clean sheet. We utilize Infrastructure-as-Code (IaC) and automated OSCAL (Open Security Controls Assessment Language) documentation tools to ensure that your system state always matches your regulatory requirements. For a founder, this means a faster path to an Authorization to Operate (ATO) and a quicker transition to revenue-generating federal contracts.
Flexible engagement and expert consulting
We understand that every startup and investment group has unique operational needs. Whether you require a full-service development team to build a platform from scratch or specialized C-level technical consulting to navigate a specific FedRAMP hurdle, Idea Usher offers highly flexible engagement models. We provide access to niche experts who can act as an extension of your internal team, offering strategic guidance on everything from cloud selection to Zero-Trust identity frameworks.
Our global reach, combined with a local compliance focus, allows us to build software that respects regional data residency and sovereign mandates while maintaining a unified global codebase. This level of expert oversight ensures that your platform is not just ready for today’s audit, but is future-proofed against the evolving regulatory landscape of 2026 and beyond.
Monetization Models for FedRAMP SaaS Products
The financial architecture of a federal SaaS product is as critical as its technical one. For an entrepreneur, the goal is to align with the government’s shift toward Category Management and Cloud Smart procurement while maintaining the high-margin predictability that investors demand. The launch of FedRAMP 20x has introduced a new level of “price transparency” in the marketplace, meaning agencies now have more data to benchmark your costs against authorized competitors.
The challenge for a founder is navigating the tension between the government’s preference for budget certainty and the industry’s push toward flexible, usage-driven revenue. In the 2026 landscape, a successful monetization strategy often involves a hybrid approach that protects your downside through annual commitments while capturing upside through tiered growth.
Subscription-based SaaS for government agencies
The traditional subscription model remains the cornerstone of federal SaaS because it fits perfectly within the Firm-Fixed Price (FFP) contract structure that government contracting officers prefer. -, however, the “per-user” or “per-seat” model is evolving into a more sophisticated Capability-Based Subscription.
- Tiered Value Baselines: Instead of a flat fee, founders are increasingly using tiers aligned with FedRAMP Impact Levels. For example, a “Base” tier might offer functionality in a Low-impact environment, while a “Premium Federal” tier provides the same features within a High-impact / Level 5 enclave with enhanced support. This allows you to charge a premium for the higher operational costs of maintaining a more rigorous security boundary.
- The Multi-Year Anchor: Federal agencies often have “color of money” requirements that favor multi-year appropriations. Offering a 3-to-5-year subscription with a locked-in FedRAMP maintenance fee provides the long-term Annual Recurring Revenue (ARR) that significantly inflates a company’s valuation during a liquidity event.
Licensing and enterprise contracts
For larger agencies or department-wide deployments, individual subscriptions become administratively burdensome. -, we are seeing the rise of Agentic Enterprise License Agreements (AELAs). As agencies deploy more AI-driven automation, the “human seat” is no longer the primary unit of value.
- Agency-Wide Unlimited Access: An ELA allows an entire agency (e.g., the Department of Transportation) to use your platform without worrying about license management for every new employee. This creates “stickiness” and makes it nearly impossible for a competitor to displace you.
- Co-operative Purchasing: Under the FedRAMP 20x Marketplace rules, smaller agencies can now “piggyback” on the enterprise contracts of larger ones. As a founder, securing one major ELA can act as a “Lead Contract,” allowing other agencies to buy off your existing schedule without a new, lengthy procurement cycle.
- The “Maintenance” Premium: Enterprise contracts in the federal space typically include a dedicated Continuous Monitoring (ConMon) Surcharge. This covers the cost of the monthly 3PAO reporting and automated telemetry required to keep your ATO active, ensuring that your compliance costs don’t eat into your software margins.
Usage-based pricing for cloud services
The most significant shift – is the adoption of Consumption-Based Monetization, mirrored after the billing models of AWS and Azure. This is particularly relevant for AI, data analytics, and storage platforms where the value is tied to the volume of work performed rather than the number of people logged in.
- Credit-Based Drawdowns: To reconcile “variable usage” with “fixed federal budgets,” many founders use a “Pre-paid Credit” model. An agency purchases $500,000 worth of “processing units” at the start of the fiscal year. As they run AI queries or store data, those credits are deducted. This gives the agency the budget certainty they need while allowing the founder to capture the high-volume usage of a power user.
- The “FinOps” Requirement: If you choose a usage-based model, your platform must include an Authorized Spend Dashboard. Federal managers are legally required to prevent “anti-deficiency” violations (spending more money than was appropriated). A platform that can automatically “throttle” usage or alert a manager before they hit their budget limit is a prerequisite for any consumption-based contract -.
- Predictability Caps: To win over skeptical procurement officers, savvy entrepreneurs are offering Hybrid Contracts: a base subscription fee for “essential” usage combined with a capped usage fee for “burst” capacity. This protects the government from runaway costs while ensuring the SaaS provider is compensated for the extra compute load.

Future Trends in FedRAMP Software Development
As we move through 2026, the landscape of federal cloud security is undergoing its most significant transformation since the inception of the program. The legacy era of manual, paper-heavy compliance is being aggressively retired in favor of the FedRAMP 20x framework and the Consolidated Rules 2026 (CR26). For investors and entrepreneurs, this represents a fundamental shift in how value is created and protected within the federal marketplace. The goal is no longer just to achieve a point-in-time authorization, but to maintain a state of continuous, machine-verifiable security.
This new paradigm favors cloud-native platforms that can operate with agility while meeting the uncompromising demands of the U.S. government. We are seeing a move toward sovereign-first architectures where compliance is not an afterthought but a core performance metric. As federal agencies accelerate their migration away from legacy on-premise systems, the demand for platforms that can seamlessly integrate with automated government oversight tools is skyrocketing, creating a massive opportunity for firms that can master the new compliance-as-code standards.
AI-driven compliance automation platforms
The release of RFC-0024 in early 2026 has officially mandated the transition to machine-readable OSCAL (Open Security Controls Assessment Language) for all new authorizations. This marks the end of the 800-page static System Security Plan (SSP). In its place, we are seeing the rise of AI-driven compliance automation platforms that act as a digital twin for your security posture. These tools don’t just store documentation; they ingest live telemetry from your environment and map it to NIST 800-53 controls in real-time.
- Deterministic Evidence over Narratives: By the September 30, 2026 deadline, every new federal platform must provide Key Security Indicators (KSIs). Instead of a human auditor reading a description of your firewall rules, a machine will verify the actual configuration data. This reduces the audit timeline from months to weeks, allowing authorized vendors to capture agency budgets with unprecedented speed.
- Predictive Risk Management: Advanced automation platforms are now using machine learning to predict configuration drift before it leads to a compliance violation. For an investor, this significantly lowers the operational risk of an Authorization to Operate (ATO) being suspended due to human error, ensuring that the recurring revenue from government contracts remains stable and protected.
Zero trust architecture adoption
Zero Trust is no longer a buzzword; it is the mandatory architectural standard for federal systems under OMB M-24-15. The transition to a Zero Trust Architecture (ZTA) requires a complete rethink of the network perimeter. -, successful FedRAMP platforms are those that have eliminated the concept of an “internal” trusted network in favor of continuous, identity-centric verification at every layer of the stack.
- Identity as the New Perimeter: Modern federal apps must support phishing-resistant Multi-Factor Authentication (MFA) and dynamic, attribute-based access controls. Every request whether from a human user or an AI agent must be explicitly verified based on the sensitivity of the data and the security posture of the device.
- Micro-segmentation and Least Privilege: The 2026 standards demand that applications be broken down into micro-segments where every service-to-service communication is encrypted and authorized via Mutual TLS (mTLS). This ensures that even if one component of the platform is compromised, the attacker cannot move laterally to access sensitive government data, fulfilling the federal mandate to assume breach as a baseline operational state.
Growth of FedRAMP Moderate and High demand
While Low-impact (LI-SaaS) was the initial testing ground for automation, 2026 has seen a massive surge in demand for Moderate and High Impact authorizations. This growth is driven by the federal government’s pivot toward Sovereign AI and specialized data analytics. Agencies are no longer content with basic productivity tools; they are seeking hardened platforms capable of processing Controlled Unclassified Information (CUI) and mission-critical intelligence data.
- The High Impact Moat: For entrepreneurs, achieving a FedRAMP High authorization – creates one of the most defensible competitive moats in the technology industry. The requirements for hardware-backed encryption (FIPS 140-3) and dedicated sovereign enclaves are high, but the reward is access to the multi-billion dollar defense and national security budgets that are largely insulated from commercial economic cycles.
- Phase 2 and 3 Rollouts: As the FedRAMP PMO completes the Phase 2 Moderate pilot in mid-2026, the pathway for Moderate-impact SaaS is becoming more standardized and predictable. This allows firms to plan multi-year federal expansion strategies with a level of budget certainty that was previously impossible. Investors are increasingly looking for platforms that can prove their readiness for these higher impact levels as a prerequisite for Series B and C funding rounds.
How to Get Started with FedRAMP Software Development
Entering the federal market – requires a departure from traditional “build-first” strategies. Under the Consolidated Rules 2026 (CR26), the U.S. government has prioritized machine-readable validation and Zero Trust architectures. For investors and entrepreneurs, the window for capturing market share has widened, but the technical bar for entry is higher. Success now depends on producing deterministic telemetry from day one, ensuring your platform is ready for the automated review cycles of the FedRAMP 20x framework.
Validate your idea with compliance experts
Before committing capital, a rigorous Gap Analysis is essential to select the correct Certification Class (A-D). -, most SaaS providers target Class C (Moderate), which covers the majority of federal workloads. Experts help define a surgical System Security Boundary to prevent “scope creep” that can inflate audit costs.
This phase is about making critical infrastructure decisions such as choosing AWS GovCloud or Azure Government and identifying technical showstoppers like non-compliant third-party APIs. Proper validation at the seed stage ensures that your FIPS 140-3 encryption and identity frameworks are built to federal standards, avoiding the million-dollar re-architecture typical of “bolt-on” security attempts.
Build a roadmap aligned with FedRAMP
Your 2026 development roadmap must be OSCAL-native (Open Security Controls Assessment Language). Static Word documents are being retired; new submissions must be machine-readable by the September 30, 2026 deadline. Your roadmap should prioritize Balance Improvement Releases (BIRs), which provide pre-validated security blueprints to accelerate your timeline.
Transitioning to a SecDevOps culture is mandatory. Every sprint must produce Key Security Indicators (KSIs) automated logs that prove your security controls are functioning in real-time. This approach turns your compliance posture into a living, auditable asset that satisfies the government’s shift toward Continuous Monitoring (ConMon) and reduces the friction of annual assessments.
Partner with Idea Usher for development
Building for the federal sector requires a partner who treats regulatory engineering as a core performance metric. Idea Usher specializes in architecting FedRAMP-certified assets that leverage inheritance mapping to lower your total cost of ownership. We integrate FIPS-validated modules and Zero Trust identity directly into your codebase, ensuring your platform is secure by design.
By partnering with us, you gain access to a team that navigates the complexities of CR26 and 20x automation on your behalf. We provide the technical oversight necessary to move through Third-Party Assessment Organization (3PAO) audits with confidence. At Idea Usher, our goal is to help you clear the “compliance moat” rapidly, transforming a complex regulatory requirement into a powerful, revenue-generating competitive advantage.

FAQ’s
The Federal Risk and Authorization Management Program (FedRAMP) is the mandatory security standard for any cloud service used by the U.S. federal government. It provides a uniform approach to risk assessment and authorization, ensuring that cloud products are secure enough to handle sensitive federal data. In 2026, the framework has evolved into an automation-first ecosystem, prioritizing machine-readable evidence over traditional narrative documentation. This modernization, known as FedRAMP 20x, allows well-architected platforms to move from initial assessment to an Authorization to Operate (ATO) in months rather than years.
Compliance requires a platform to implement a prescriptive set of security controls based on the NIST 800-53 Revision 5 standards. The exact requirements are dictated by the system’s Certification Class (A, B, C, or D), which has replaced the legacy impact levels. Key requirements include a strictly defined System Security Boundary, the use of FIPS 140-3 validated encryption, and the implementation of phishing-resistant Multi-Factor Authentication (MFA). Furthermore, all documentation must now be submitted in OSCAL (Open Security Controls Assessment Language), ensuring that your security posture is machine-verifiable and transparent to federal auditors.
If a software platform creates, stores, processes, or transmits federal data, FedRAMP certification is legally mandatory. Under the current federal mandate M-24-15, agencies are strictly prohibited from using unauthorized cloud services for any official business. While there are narrow exceptions for low-risk ancillary tools, the vast majority of B2B SaaS products targeting the government must hold a valid FedRAMP Certified label. For founders, this certification acts as a powerful market entry tool and a formidable competitive moat, as it signals a level of security maturity that most commercial-grade competitors cannot match.